Authors: Infoblox Threat Intel and Confiant
Executive Summary
Cloaking—the act and art of hiding a website’s true nature—is a critical component of cybercriminal operations today. Threat actors use domain cloaking, implemented through traffic distribution systems (TDSs) and cloaking kits, to evade content restrictions in advertising, for precision targeting of victims for malware and scams, and to protect themselves from each other. Some actors develop their own TDS or purchase access to wholly criminal operations like BlackTDS, 404TDS, and ParrotTDS. But many avail themselves of commercially available software. After all, cybercrime is like any other economy: Why build when you can use highly sophisticated products developed by others?
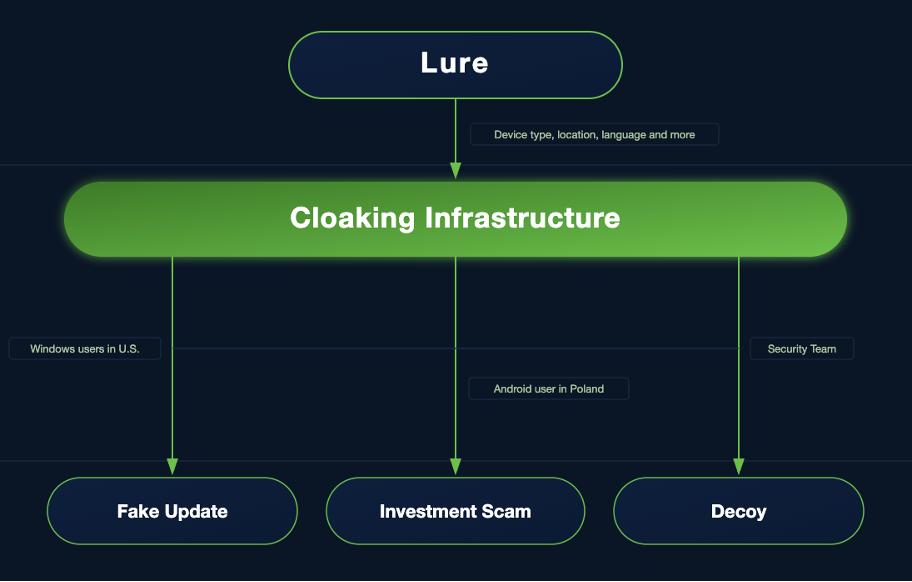
Keitaro Tracker, sometimes referred to as Keitaro TDS, is an advertising performance tracking platform that has been frequently observed in malicious campaigns and abused by threat actors, though it certainly isn’t the only commercial tracker used in this way. It has gained attention across the security community because of its adoption by some of the most notorious criminal actors over the last decade. In the past few years, it has been a signature of TA2726, who uses Keitaro to deliver traffic to SocGholish (TA569) for their fake browser update campaigns. Website visitors who do not meet the targeting requirements for SocGholish are dumped out to other affiliate advertising platforms or fed decoy pages. Beyond TA2726, Keitaro has been reported in security literature dozens of times, most recently in spam campaigns using Jira to target government entities.
While it is “well known” that Keitaro is abused by threat actors, there has never been a longitudinal study to understand the nature of this abuse. Infoblox and Confiant collaborated over the last six months to understand how threat actors use the tracker based on our complementary views of the environment. Confiant can see across the advertising chain, while Infoblox focuses on how threats appear in DNS, using spam and website content to inform our understanding of the landscape. We discovered early on that the Keitaro instances we observed in attacks showed little overlap, making a combined story not just more compelling, but vast.
We examined four months of data starting October 1, 2025, to determine how much of that use was malicious. During this time, we detected thousands of instances of malicious Keitaro cloaking content ranging from investment scams to information stealers. Traffic to the instances was driven from compromised websites, spam, social media, and advertising. The level and persistence of abuse is quite staggering. Keitaro is a feature-rich, self-hosted tracker that can be spun up in a few minutes on multiple hosting platforms, likely making it attractive to use. We found approximately 15,500 domains actively used for malicious Keitaro instances during this time, with about 9,000 of those registered before their use. These were used in advertising campaigns seen by Confiant, but also included in spam emails, embedded in compromised websites, and linked through other traffic sources.
Investment scams dominated the threats we saw. A recent trend in this type of scam is the use of AI as a central marketing hook: pages routinely claim “advanced AI” or “AI‑driven algorithms” that automate trading and promise outsized returns. Several actors also incorporate deepfake imagery or video to boost perceived credibility. We additionally observed indicators of programmatic use of generative AI to mass‑produce headlines, copy, and visuals that are deployed as lure pages and ad creatives.
Aside from domain cloaking, Keitaro’s conditional routing based on device characteristics allows operators to create complex traffic flows. We analyzed thousands of attack instances to characterize the flows used in these types of scams. Figure 1 summarizes the most common flows from geo + user agent cohorts to the languages used by the landing page. We can see that in these attacks, regardless of visitor location and device type, the final lure is shown in a limited number of languages, predominantly Russian and English. This might indicate targeting by the attacker or limited capabilities on their part. While many of the campaigns are global, there are notable threat actors, particularly ones observed by Confiant in the advertising ecosystem that specifically target the United States.
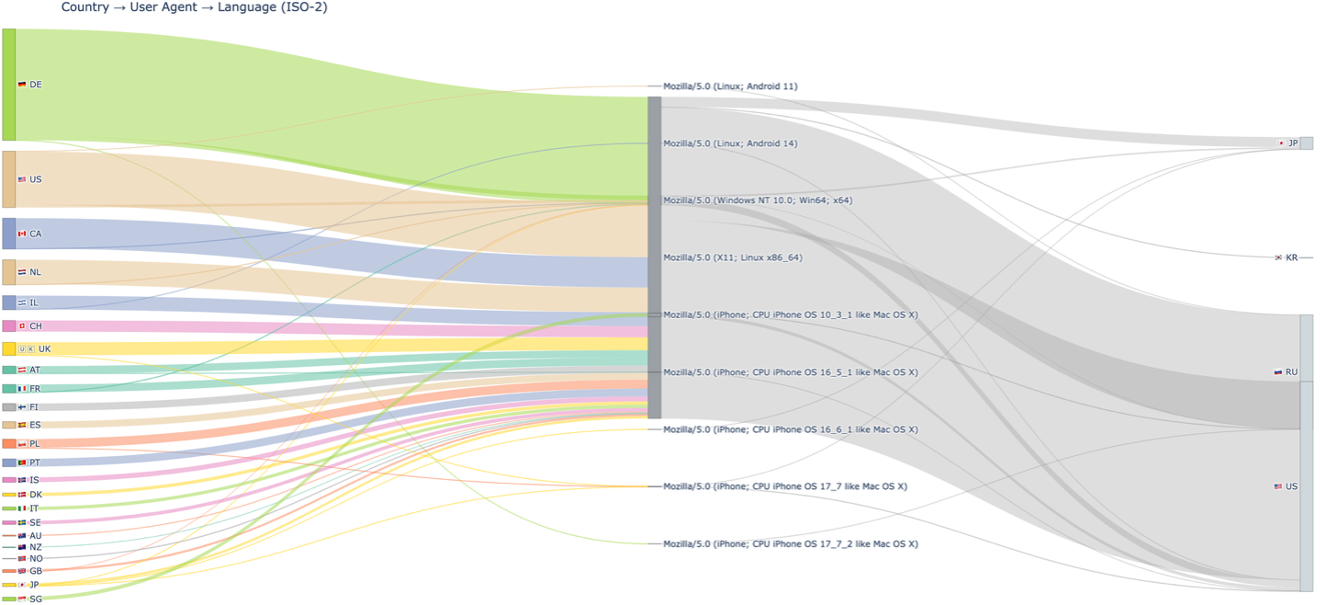
Figure 1. Keitaro traffic filters for AI-driven campaigns
We also set out to determine how responsive Apliteni, the company that developed and sells Keitaro Tracker, was to abuse reporting. After all, Keitaro has been used by bad actors over such a long period of time, it begged the question of whether the company turned a blind eye to abuse: were they a bulletproof tracker, so to speak? Since August 2025, we have reported over a hundred domains. The company responded quickly and thoroughly to each of our requests. As a result, over a dozen threat actors’ accounts were canceled. The Keitaro Tracker licensing terms prohibit, among other things, “misleading” content. This allows the company to terminate an instance using a tracker for malicious cloaking purposes. In many cases, the domains we observed were not valid licenses. Through multiple exchanges based on the activity we saw and the customer information the Keitaro team held, we verified that TA2726 and other malware actors were using illicit copies of the tracker.
While we took a deep dive into Keitaro Tracker, this multi-part publication is intended to highlight the depth and breadth of cloaking in the threat landscape. Other commercial trackers, like Binom, are also highly abused and this research is not intended to implicate Keitaro more than these others. Indeed, our collaboration with Keitaro led to new discoveries that would not have been possible otherwise. Hyrhorii, head of Trust and Safety, told us regarding this reporting, “At Keitaro, we are dedicated to maintaining a professional and secure environment for legitimate marketing. Our strategy is built on both reactive and proactive measures: while we promptly act on external abuse reports, we also invest heavily in internal monitoring to identify and neutralize malicious patterns before they can impact the ecosystem. The fact that actors ‘stay down’ after our intervention confirms that our approach is working. We value our collaboration with Infoblox, as proactive synergy between software vendors and cybersecurity experts is the only way to effectively protect industry reputation and user safety.”
This is the first of three blogs sharing the results of this study. The use of AI in illicit activity is growing, and campaigns fueled by Keitaro abuse are no different. In this blog we will report on the subset of threat actors who have leveraged AI in their campaigns, most of which were investment scams. The next blog will provide a survey of the many other subsets of actors both teams found. The final blog will dive into how cybercriminals have weaponized the features and functionalities of Keitaro’s software for nefarious purposes, and discuss our collaboration with the vendor on abuse.
While we are using real-world examples to tell the story—this is not just another blog about AI or investment scams. The key takeaway here is that threat actors are using domain cloaking to drive an endless torrent of malicious content to users of all types, in all corners of the globe, and that Keitaro is one tool they commonly choose in these campaigns. While Apliteni can, and has, responded to abuse reporting, the sheer volume and diversity of the threats, not to mention the ingenuity and license theft, makes these technologies a persistent, underreported challenge for defenders.
Confiant secures the digital advertising supply chain and protects many major advertising exchanges, platforms, and publishers. Their visibility of close to 90 billion ad impressions a month on publisher sites is derived from thousands of client-side integrations that block malvertising attacks. This product suite also collects telemetry on threat activity seen in the wild and serves to complement the view Infoblox Threat Intel has via DNS, spam, and website scans.
Investment Scams and AI
The largest category of threats we have identified abusing Keitaro services is investment scams. While both Infoblox and Confiant found this type of fraud to dominate our detections, the threat actors we see are different due to our visibility and focus. In a previously published blog, Infoblox highlighted the recurring tactics, techniques, and procedures (TTPs) that define these operations, and those patterns remain consistent:
- Registering large numbers of domains algorithmically over time, a technique we refer to as registered domain generation algorithms (RDGAs)
- Reusing nearly identical web forms to capture user information
- Deploying kits that produce uniform website structures
- Relying on fabricated news articles or endorsements to appear legitimate
We will start by sharing some of the unnamed actors that Infoblox tracks in this space, many of whom leverage social media, especially Facebook Ads, to lure victims. Whereas we’ve seen AI used to generate pages for years, fraudsters are now incorporating AI as an advantage in using their fake trading platform. Figure 2 shows the different templates used by an actor we track that runs these types of investment scam campaigns.
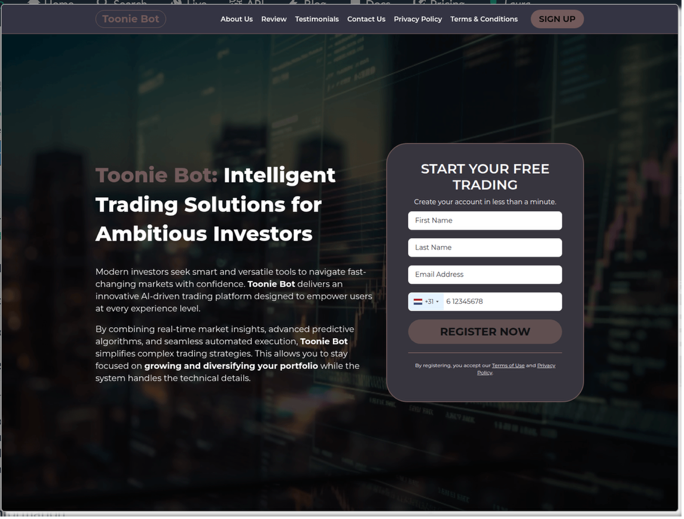
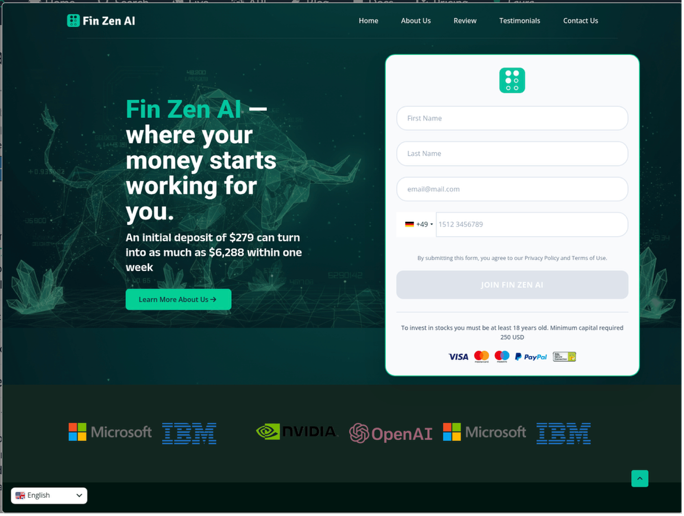

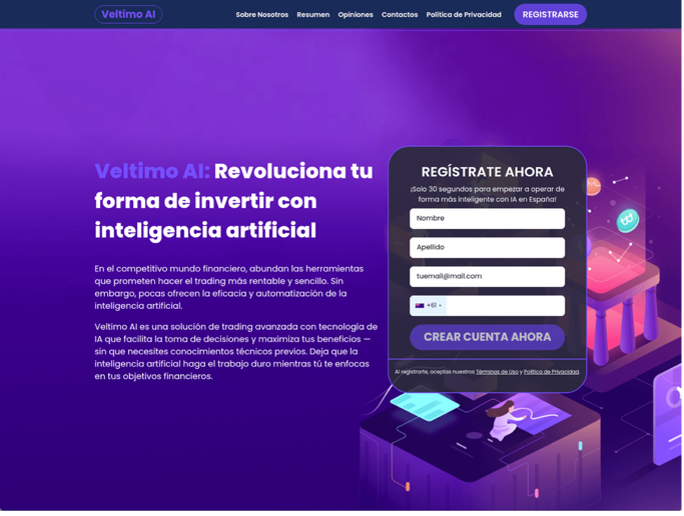
Figure 2. Investment scam landing pages featuring AI‑powered trading platforms, sharing a similar structure and a common embedded web form used to collect victim details. Image credit: urlscan.io
The second threat actor also runs an AI‑themed investment scam, but its website template design favors a more minimalistic style with a white background (Figure 3). Despite the shift in style, the underlying pattern remains the same: promoting AI‑powered trading as a lure to draw victims into an investment scam. It promises market‑beating, low‑risk automated returns and pads the pitch with meaningless buzzwords, like “blockchain.” A web form collects visitor contact details. With these kinds of scams, the threat actor typically impersonates an “account manager” and bombards victims with phone calls to secure an initial investment. Based on observed language distribution, the actor appears to primarily target English- and German-speaking audiences, with additional targeting of Japanese, Italian, Dutch, French, Spanish, and Portuguese speakers.

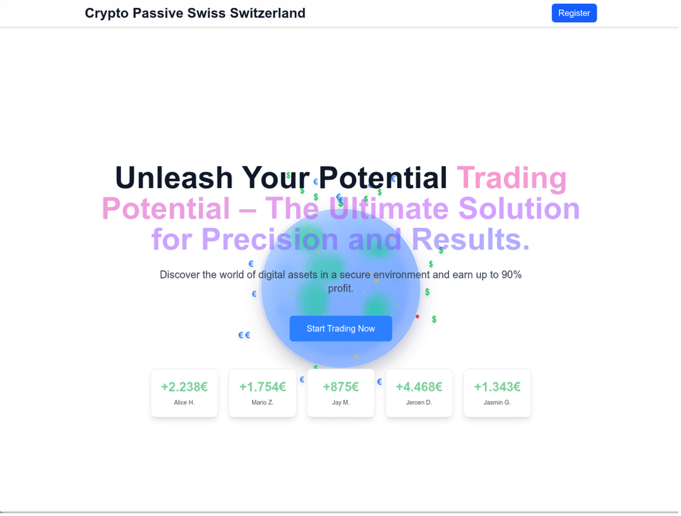

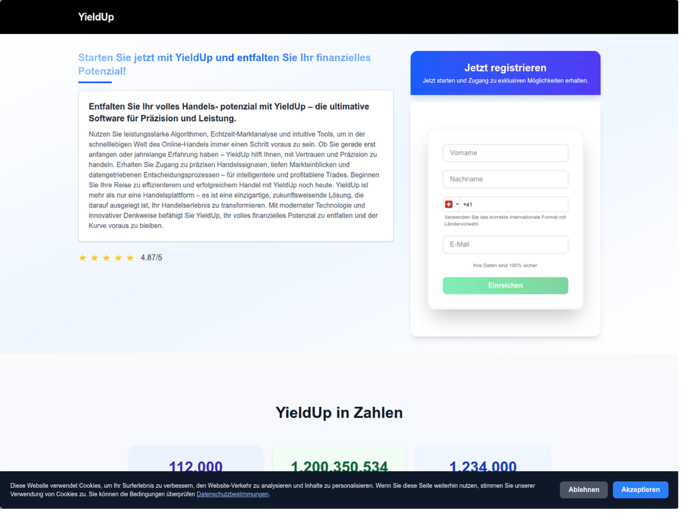
Figure 3. Investment scam landing pages linked to a separate threat actor that were observed promoting AI‑powered trading platforms and near‑five‑star reviews. Image credit: urlscan.io
The next threat actor appears to rely on AI‑themed fake news articles to promote their investment scheme. Rather than fabricating celebrity endorsements, these pages present AI itself as the trusted authority, framing it as a transformative technology that enables effortless, expert‑level trading for everyday users. Across versions of the site presented in multiple languages, the content consistently pairs AI‑related imagery with narratives claiming that AI simplifies complex financial decisions (Figure 4), illustrating how the actor adapts the same core message for different audiences. The actor also uses RDGA domains such as those in Table 1 for their campaigns.

Figure 4. AI‑themed fake news pages used by an unnamed threat actor to promote investment scams by positioning AI as a trusted authority across multiple languages. Image credit: urlscan.io
| Lumitex + AI or + X suffix | ATT prefix/suffix | Other |
|---|---|---|
| lumitexaihub[.]com lumitexaicloud[.]com lumitexsyncai[.]com lumitexstackai[.]com lumitexinsightai[.]com lumitexconnectx[.]com lumitexlaunchx[.]com lumitexgridx[.]com lumitexbasex[.]com lumitexflowx[.]com |
echoatt[.]com rocketatt[.]com tradefyatt[.]com profitlyatt[.]com igniteatt[.]com autopilotatt[.]com wizardatt[.]com quietbotatt[.]com autotradeatt[.]com attgenius[.]com |
tradingideasai[.]com tradingideasfromai[.]com star-boostmedia[.]com |
| Table 1. RDGA domain name patterns used by an unnamed investment scam actor who cloaks campaigns with Keitaro | ||
For the set of pattern domains listed in the “Other” column of Table 1 above, the actor relies heavily on subdomains of the RDGAs to control the language of each landing page. The leading label in the hostname (for example, tr, au, br, za, swe, mx, pl) corresponds directly to a specific locale or language group, indicating some of the actor’s targeted languages. When a user is routed to one of these subdomains, the website automatically serves content in the associated language, allowing the actor to reuse the same infrastructure while still presenting localized material tailored to each region. Table 2 shows what these subdomains look like.
| Hostname | Language |
|---|---|
| au.star-boostmedia[.]com | English (Australia) |
| br.star-boostmedia[.]com | Portuguese (Brazil) |
| can.star-boostmedia[.]com | English (Canada) |
| mx.star-boostmedia[.]com | Spanish (Mexico) |
| pl1.tradingideasai[.]com | Polish |
| swe.star-boostmedia[.]com | Swedish |
| tr.star-boostmedia[.]com | Turkish |
| za.star-boostmedia[.]com | English (South Africa) |
| Table 2. Observed subdomains and their associated languages. | |
FaiKast
Confiant has tracked FaiKast (derived from “Fake AI News Broadcast”) since May 2025. FaiKast is a threat actor that leverages AI-generated deepfake videos to impersonate recognizable television news anchors and public figures (Figure 5). The deepfakes create an illusion of legitimacy and urgency around fraudulent investment schemes. FaiKast has been observed entering the AdTech supply chain primarily through Bigo Ads. Bigo Ads has also fallen under additional scrutiny in this new research on their SDK by Buchodi.

Figure 5. FaiKast news anchor deepfakes
Typical FaiKast delivery TTPs are as follows:
Stage 1 (Lure): AI-generated video ads featuring deepfake news anchors are served through the ad ecosystem, localized to match the target audience’s language, currency, and regional news cycle. Geos targeted include several European countries such as France and the U.K., as well as Canada, Japan, and Kazakhstan.
Stage 2 (Landing): Victims who click through are taken to near-perfect replica sites of legitimate news outlets (e.g., CBC News). These fake pages include fabricated reader comments, images of real public figures (e.g., Canadian PM Mark Carney), and urgent calls-to-action to sign up for fraudulent cryptocurrency platforms with names like Pyravelon, Tyveralon, and Quantum AI. See Figures 6 and 7 for examples.
Stage 3 (Conversion): Victims are funneled to fake government assistance pages and fraudulent investment portals.
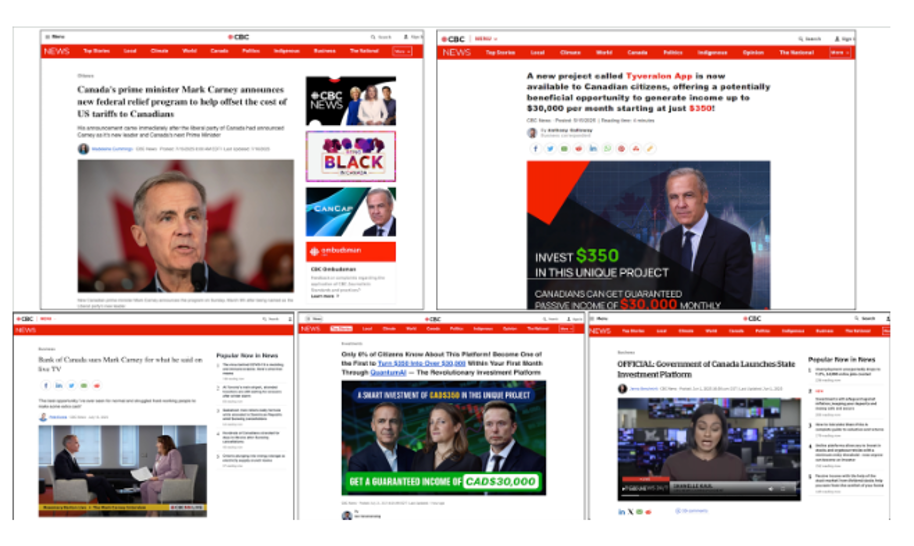
Figure 6. FaiKast landing page samples impersonating CBC News
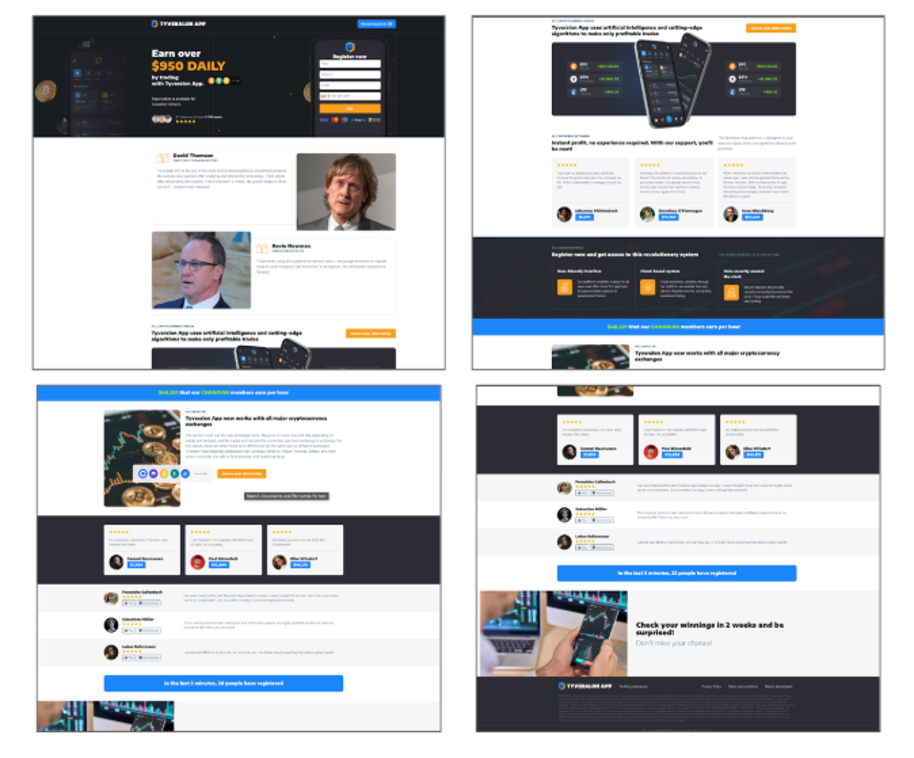
Figure 7. Additional FaiKast landing page samples: calls-to-action to sign up for fake cryptocurrency platforms
WickedWally
WickedWally is a deceptive affiliate marketing cluster targeting specific U.S.-based audiences, such as senior citizens and those in need of social assistance programs with lures of debt relief, grocery allowances, Medicare benefits, and funeral expenses. This actor has been active and tracked by Confiant since at least 2024.
WickedWally uses generative AI deepfake video ads, often designed to look like news reports, that leverage current events and opaque language such as: “Due to the USA tariffs release, you can erase your credit card debt for free until this Saturday” (see Figure 8 for an example).

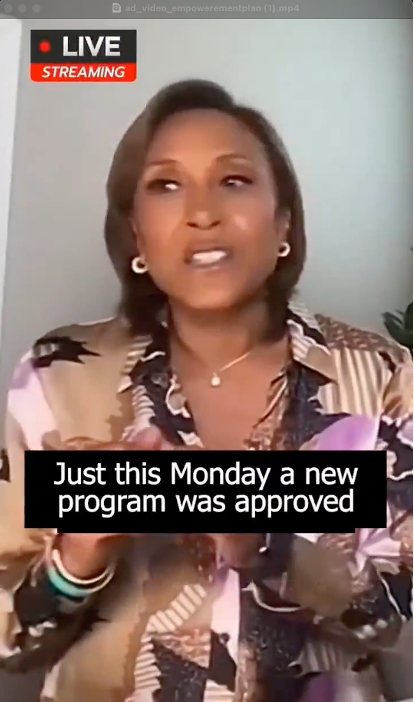
Figure 8. WickedWally ad sample impersonating a CNN news broadcast for investment scam domain empowerementplan[.]com
A common landing page WickedWally uses is a fake chatbot—a low-friction chat with an “agent” to “qualify” the victim for a fake benefit and build a false sense of legitimacy. They prompt users to call various toll-free numbers with prefixes such as 1-844, 888, etc. which route to unverified third-party call centers that urge people to share their personal and/or financial information. See Figure 9. Other landing pages feature fake reviews and urgency, fake logos, and totally unrealistic claims.
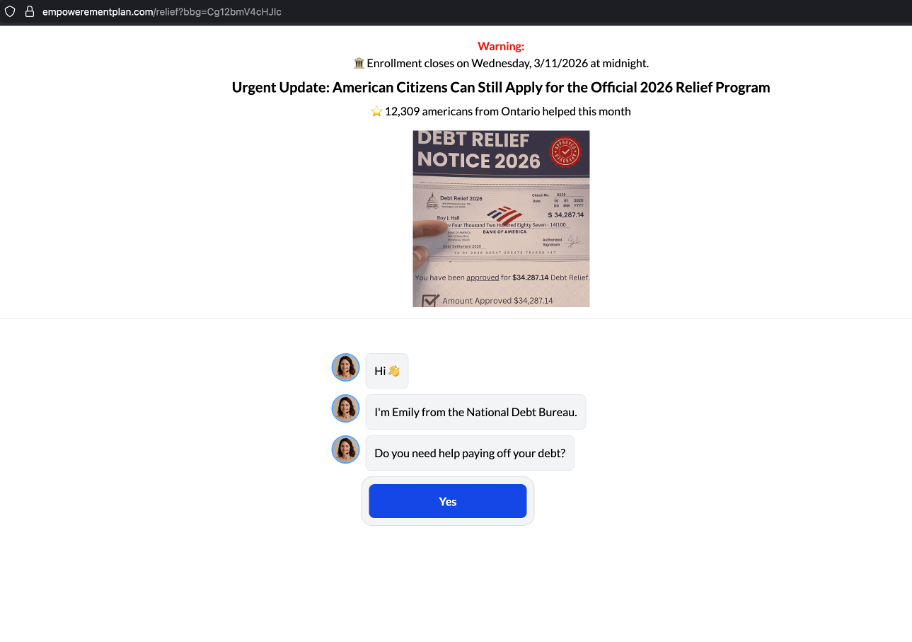
Figure 9. WickedWally landing page sample for empowerementplan[.]com, featuring a fake debt relief lure
Instead of using cloaking, these campaigns attempt to slip through by blending in with legitimate lead-generation marketing. Despite this approach, Keitaro still plays a critical role in the delivery infrastructure, ostensibly for endpoint routing and campaign tracking. In our observations, this actor repeatedly used Keitaro Tracker as part of its campaign delivery chain, making it a useful signal when identifying related activity.
Tech Support Scams (Unattributed)
Malvertising remains a fertile source for uncovering tech support scams (TSSs). Confiant tracks multiple actors in this space that exhibit closely aligned TTPs. While cloaking is common, Keitaro is not frequently observed in these chains; but a notable exception surfaced last October. In that campaign, a TSS operator blended AI‑generated assets into lure sites, a technique that increases perceived legitimacy and scales with production. Keitaro was then used to conditionally route visitors from the lures to scam landing pages or other payloads based on signals such as IP, geo, user agent, and referrer, while diverting non‑targets to benign content. The lures impersonated popular brands or topics and used broad commerce keywords (e.g., Taylor Swift, shoes, pillows, board games) to cast a wide net across search and ad inventory. This programmatic approach lets the actor mass‑produce pages that match diverse queries, extend SEO coverage, and sustain a steady inbound stream into the support‑scam funnel. This actor is an early adopter of AI technologies, including OpenAI’s DALL-E text‑to‑image generator. Confiant has been tracking this activity since November 2023.
Typical TSS actor TTPs are as follows:
Stage 1 (Lure): Native display ads are served into programmatic display ad slots on publisher pages. Ad creatives feature prominent green “START” buttons, IQ test prompts, fake download offers, or clickbait topics (gardening tips, moving companies, lifestyle content). TSS actors can operate within locked-down native ad templates, which do not allow custom JavaScript execution in the ad itself. Ads are increasingly sophisticated, evolving from simple button-style creatives to more developed ad text incorporating calls to “watch,” “learn,” or “continue.” Figure 10 shows an example of these types of ads.
Figure 10. Example of a native display ad used in Stage 1
Stage 2 (Cloaking and Landing): Victims who click through land on a multi-step cloaked landing page. The first page is typically not cloaked and presents a large “CONTINUE” button, “Start Quiz,” or “Read More” prompt. This page acts as a gate to the payload. Behind the scenes, cloaking kits perform client-side fingerprinting: checking IP geolocation (U.S. targeting), user-agent (Windows vs. macOS), ASN blacklists, and the presence of click URL parameters to confirm the visitor arrived via a paid ad click. Non-qualifying traffic receives a white page, typically a benign-looking website clone like the one in Figure 11 below.
Figure 11. Cloaked white page for marrowcliff[.]org
Cloaked page themes have evolved significantly over time and are where Confiant has been seeing TSS actors using AI. Many of these themes include:
- AI-generated content pages using DALL-E images, covering diverse topics (Taylor Swift, shoes, pillows, board games)
- Fake quizzes/IQ tests (now declining)
- Cloned business websites, stolen copies of legitimate digital marketing agencies, SEO firms, and platforms like Capterra
- Cookie consent modals that auto-redirect after two seconds or upon any user interaction (accept or decline)
Stage 3 (TSS Payload): Victims who pass fingerprinting are redirected via HTTP 302 to a tech support scam page, often hosted on Azure Blob Storage (*.web.core.windows.net subdomains). These pages are short-lived and impersonate Microsoft or Apple, displaying fabricated virus alerts, trojan warnings, Windows Defender error messages (Figure 12), and fake system scans. Victims are urged to call a fraudulent support number. Scam operators then request remote access, run fake diagnostics, and demand payment via credit card, gift cards, wire transfer, or cryptocurrency. Reported individual victim losses have reached beyond US$40,000 in documented cases.
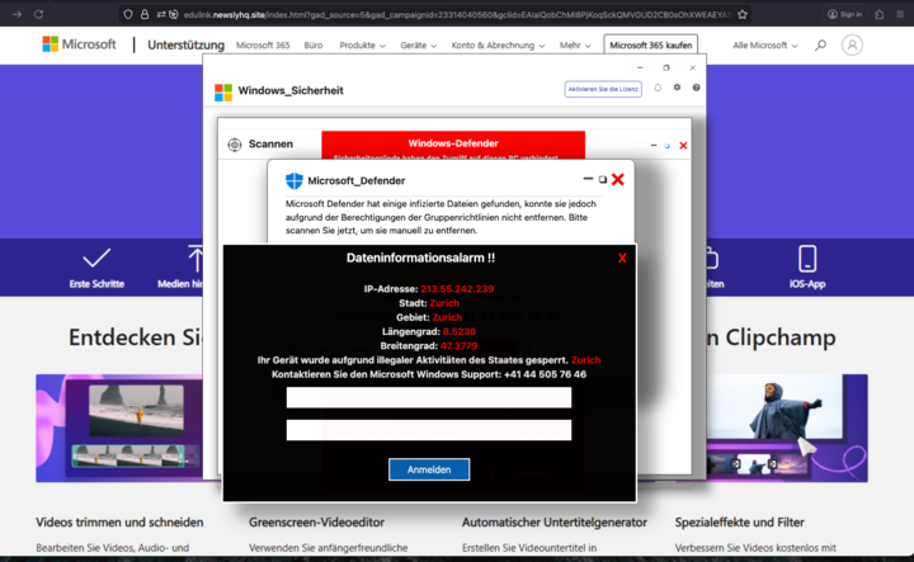
Figure 12. Uncloaked TSS fake alert, fake scan, and payment demand
TSS activity primarily targets users in the United States with fingerprinting logic specifically gating on U.S. IP ranges. Secondary targeting includes Japan (with ads in Japanese) as well as broader English and European-language markets.
FishSteaks
Our analysis surfaced some findings from FishSteaks, a mature cluster that has been active since at least March 2024, likely much longer. In recent campaigns, we’ve observed FishSteaks beginning to leverage Keitaro as a cloaking mechanism. They run campaigns that target the United States and lure victims with convincing giveaway-themed creatives impersonating popular American consumer brands.
Victims are funneled through multi-stage, gamified landing pages before arriving at a final phishing site designed to harvest personal information and credit card data. The actor demonstrates scalable operations through brand rotation, subdomain cycling, and using AI-generated placeholder assets that are swapped for brand logos as campaigns go live. Gamification techniques such as virtual prize boxes and falling confetti increase victim engagement and time-on-page, boosting conversion rates.
The screenshots in Figures 13 and 14 below show landing pages for domains 5000-giftcardswb[.]ru, active throughout October and sporadically in November, and tryhappycards[.]ru, active in December. Both campaigns leveraged Keitaro and lured victims with generic ad creatives that resembled native mobile app widgets.

Figure 13. FishSteaks fake mobile app widgets
![tryhappycards[.]ru giveaway page](https://www.infoblox.com/blog/wp-content/uploads/keitaro-ai-campaign-figure-14.png)
Figure 14. tryhappycards[.]ru giveaway page
AI as a Force Multiplier, Keitaro as the Enabler
Across all of our observational data points, we identified thousands of attacks involving Keitaro. What was alarming was the diversity and sheer volume of threat actors operating in this part of the cybercrime ecosystem. Investment scams were the most common attack category, and the most compelling subset within that was AI-driven scams. By combining an older but still highly effective investment fraud theme with modern AI technologies, actors have been able to launch large‑scale, highly convincing cyber campaigns. The approach scales and defeats conventional defenses by combining conditional traffic routing (geo/IP/ASN, user‑agent/referrer, risk‑based flows), AI‑personalized content, and cloaking that shows benign pages to scanners and persuasive lures to real users. Together, these techniques reduce the efficacy of signature and rule‑based security controls and increase conversion rates for the attackers.
Actors leaned heavily on DNS infrastructure and advertising pipelines to achieve scale and lead acquisition. Effective social engineering is critical to the success of these campaigns because many of them rely on user engagement such as submitting contact details or following instructions over the phone. Consequently, actors tune their TTPs to maximize trust and engagement, routinely deploying brand‑impersonating lookalike domains, high‑fidelity AI‑generated creatives localized to the target, and deepfake audio/video assets to simulate trusted representatives or media personalities.
Although Keitaro‑abusing attacks are often complex and far‑reaching, we are encouraged by Apliteni’s responsiveness to abuse escalations. Coordinated reporting efforts have already led to infrastructure and account takedowns, giving us a viable remediation path even as actors continue rotating domains and ad creatives.
What’s Next
Since we couldn’t come close to covering all our findings and examples here, part two (of three) will move beyond AI‑themed lures to examine other fraud schemes leveraging Keitaro and the spam and advertising pipelines that support them. We’ll also share how we used webserver fingerprinting and JA4+ to surface additional Keitaro servers and uncover malware distribution activities.
Indicators
A curated selection of indicators related to the threats discussed can be seen in the table below. A more comprehensive list of indicators can be found in our GitHub repository.
Note: These domains may be associated with inactive or stolen licenses.
| Indicators | Description |
|---|---|
| fin-zen-ai[.]com synatra-nexus[.]com toonie-bot[.]com veltimo-ai[.]com |
Domains used by an unnamed threat actor running investment scams featuring AI‑powered trading platforms. The domains are associated with the examples in Figure 2. |
| argea-ai[.]org el-camino-trader[.]com mizuai[.]org myhomequote[.]xyz nuve-ai-invest[.]vip nuvei-bot-neway[.]org nuvei-bot-neway[.]vip plumaclean[.]com powerquizmaster[.]com truenorth-yachts[.]com |
Additional sample of domains used by the same unnamed threat actor running investment scams mentioned in the row above. |
| cryptopassive-swiss-switzerland[.]org nexiroka[.]net samsosi[.]net yieldup[.]ch |
Domains used by an unnamed threat actor running investment scams. The domains are associated with the examples in Figure 3. |
| bitget-passive-income[.]com cardanocrypto[.]ch clarozenvix[.]com crypto-nsw-app-au[.]com gentlevector[.]com kyvaronedge82[.]com newton-passive-income[.]net opulatrix[.]ch owleblo[.]net wirbeldappix[.]ch |
Additional sample of domains used by the same unnamed threat actor running investment scams mentioned in the row above. |
| au[.]lpa1[.]star-boostmedia[.]com pl[.]star-boostmedia[.]com pol[.]star-boostmedia[.]com lumitexchainai[.]com |
Domains used by an unnamed threat actor running AI-themed fake news campaigns. The domains are associated with the examples in Figure 4. |
| lumitexaihub[.]com lumitexaicloud[.]com lumitexsyncai[.]com lumitexstackai[.]com lumitexinsightai[.]com lumitexconnectx[.]com lumitexlaunchx[.]com lumitexgridx[.]com lumitexbasex[.]com lumitexflowx[.]com |
Sample of domains used by the same unnamed threat actor in the row above. Domains with pattern “lumitex +AI or +X suffix” |
| echoatt[.]com rocketatt[.]com tradefyatt[.]com profitlyatt[.]com igniteatt[.]com autopilotatt[.]com wizardatt[.]com quietbotatt[.]com autotradeatt[.]com attgenius[.]com |
Sample of domains used by the same unnamed actor in the row above; domains with pattern “ATT prefix/suffix” |
| tradingideasai[.]com tradingideasfromai[.]com star-boostmedia[.]com |
Domains used by the same unnamed actor in the row above. Domains with no obvious common pattern, but leverage subdomains to determine the page’s language. |
| tryhappycards[.]ru yourluckycard[.]ru |
FishSteaks – Giveaway scams |
| marrowcliff[.]org nestledawn[.]org |
Tech Support Scams |
| empowerementplan[.]com financialmatcher[.]com |
WickedWally – Debt relief scams |
| wealthlift[.]click northernavenue[.]info fzclbsmartcbeaa[.]com mcdpwmachineylpdn[.]com funds-treasure[.]com vwyitsensorjieho[.]com funds-allowance[.]com cash-revenue[.]xyz cognithic[.]com thrygate[.]com logithrive[.]com yoxjsensordkzb[.]com ggkngpssanil[.]com zoizagricultureciva[.]com tmgmaiwwta[.]com |
FaiKast – Gen AI broadcast persona impersonators |








