Authors: David Brunsdon, Darby Wise
Executive Summary
CAPTCHAs, the mundane tasks where we demonstrate our ability to select bicycles or distinguish chihuahuas from blueberry muffins, are increasingly being weaponized to trick users into performing actions with unexpected consequences. Fake CAPTCHAs are commonly associated with ClickFix attacks but have also been leveraged in other kinds of campaigns, including those we’ve documented in our blog on malicious push notifications. One way we’ve observed fake CAPTCHA pages used in campaigns is related to a telecommunications fraud scheme known as international revenue share fraud (IRSF).
Over a year ago, we encountered a website employing an unusual technique for distinguishing humans from bot traffic: it required us to send SMS messages to proceed. Only more recently did we realize how these underreported scams work. When the user follows the instructions, the messages are sent internationally and result in charges on the victim’s phone bill, with a share of that revenue going to the actor who leases the phone numbers and operates the fake CAPTCHA site.
Digging further, we found that this operation has existed since at least June 2020 and uses several tricks to ensnare victims, such as socially engineered lures and back button hijacking. During our research, we observed the use of 35 phone numbers spanning 17 countries, including those known to have high termination fees, such as Azerbaijan, Egypt, and Myanmar.
The fake CAPTCHA has multiple steps, and each message crafted by the site is preconfigured with over a dozen phone numbers, meaning the victim isn’t charged for just a single message—they’re charged for sending SMSs to over 50 international destinations. This type of scam also benefits from delayed billing, as the ‘international SMS’ charges often appear on the victim’s bill weeks later and the experience with the fake CAPTCHA has been long forgotten. In our experience, the process generated 60 SMS messages, which could cost a user $30; these are small amounts individually, but they could quickly add up for the threat actor.
Our investigation revealed a sophisticated, multi-stage fraud operation that demonstrates the convergence of two critical threats: IRSF and malicious traffic distribution systems (TDSs). While telecom companies have long understood IRSF as a significant source of revenue loss, this research shows that TDS infrastructure, the same systems that direct users to scareware or malware, also funnels victims into SMS scams at scale. The TDS infrastructure enables precise victim targeting while obscuring the malicious landing pages from security researchers and automated detection systems.
The campaigns also incorporate back button hijacking, wherein a site interferes with the browser’s history and prevents users from returning to a previous “safe” site when they hit the back button. Google recently announced a ban on the use of the technique, calling it a malicious practice.
This operation defrauds both individuals and telecommunication carriers simultaneously. Individual victims face unexpected premium SMS charges on their bills and would have difficulty identifying and reporting the fraud when it originates from such an unexpected source. Telecom carriers pay revenue share to the perpetrators while likely absorbing the losses from customer disputes or chargebacks. The TDS-driven distribution across multiple countries and phone numbers makes it nearly impossible for an individual carrier to see the full scope of the fraud affecting themselves and their customers, thereby allowing the operation to persist undetected across a fragmented regulatory landscape.
And so, unfortunately, it needs to be said: Do not send a text to confirm you are human.
On International Revenue Share Fraud
IRSF is a telecommunications fraud scheme where criminals exploit the international call and SMS termination fee system to generate fraudulent revenue. When you send an international SMS, your carrier pays a termination fee to the destination country’s carrier to complete the connection, with rates that can cost pennies or much more, depending on the receiving country. In IRSF schemes, fraudsters register phone numbers in countries with high termination fees or lax regulations, like Azerbaijan, Kazakhstan, or certain premium-rate number ranges in Europe; and establish revenue-sharing agreements with local telecom providers.
When victims are tricked into calling or sending SMS messages to these numbers, the fraudster receives a portion of the termination fee. IRSF is one of the most lucrative and persistent forms of telecom fraud globally. According to FTI Consulting’s 2025 Global Fraud Loss Report for the Global Leaders Forum, artificially inflated traffic (AIT), which includes traffic generated through IRSF schemes, is the most financially damaging type of messaging fraud, with 50% of telecommunications carriers reporting high financial losses and 54% reporting high traffic volumes. With global fraud losses that are measured in billions annually, IRSF is a big deal.
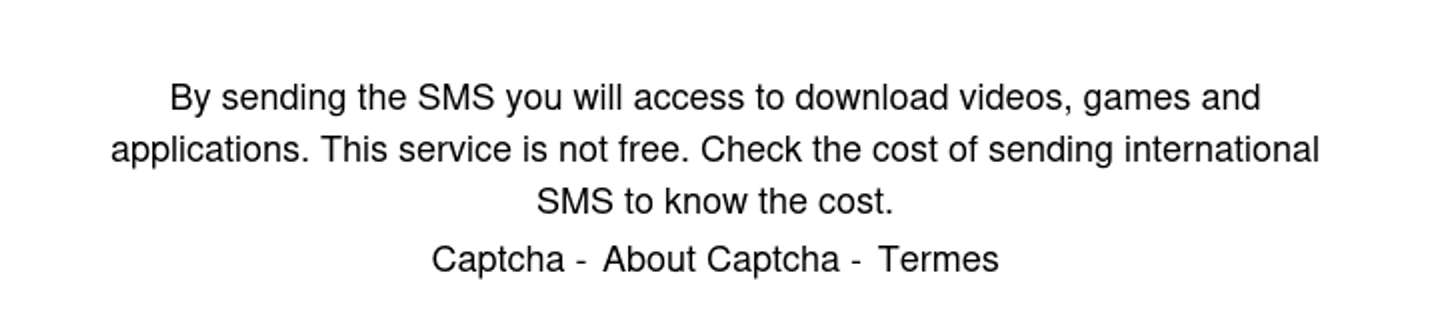
When encountering this scheme, the user will see a fake CAPTCHA and be prompted several times, with different CAPTCHA images, to send SMS messages. Figure 1 shows a partial sequence recorded on our research device in February 2025, and video of a full “user experience” is here.
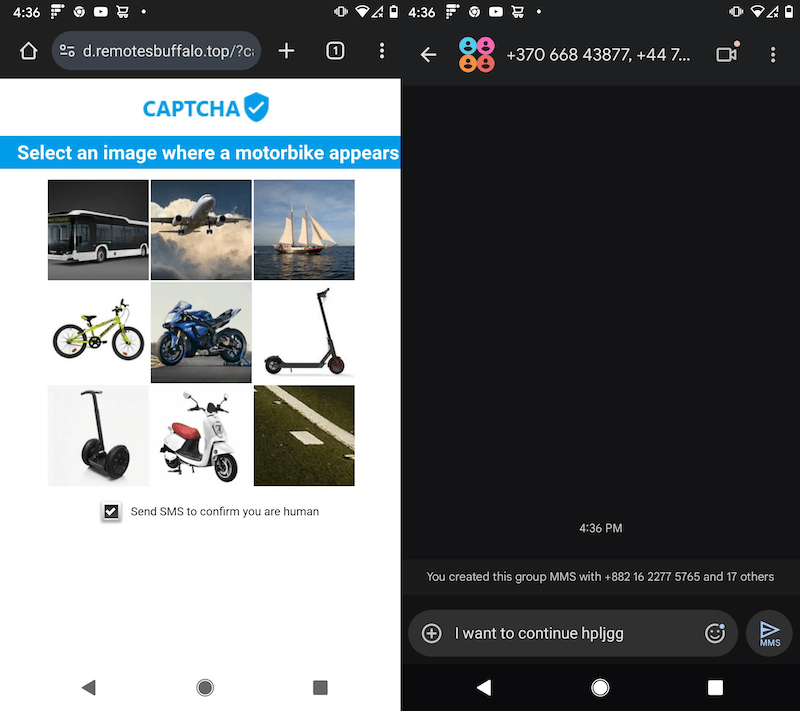
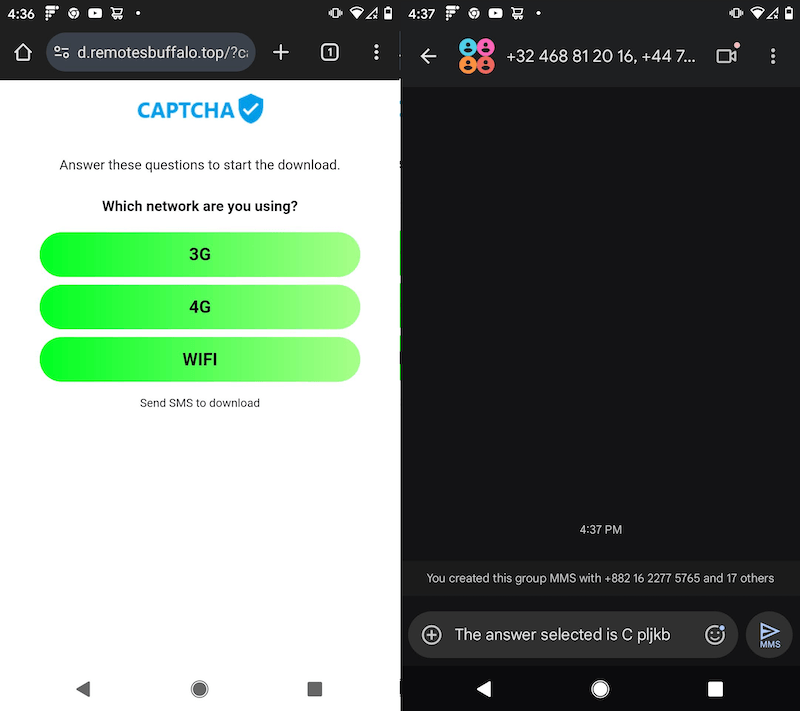
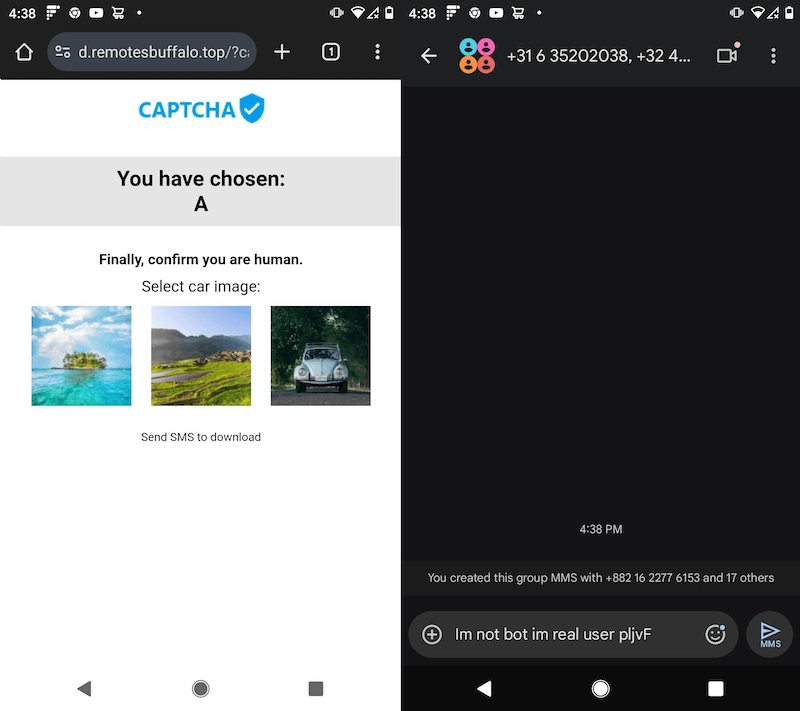
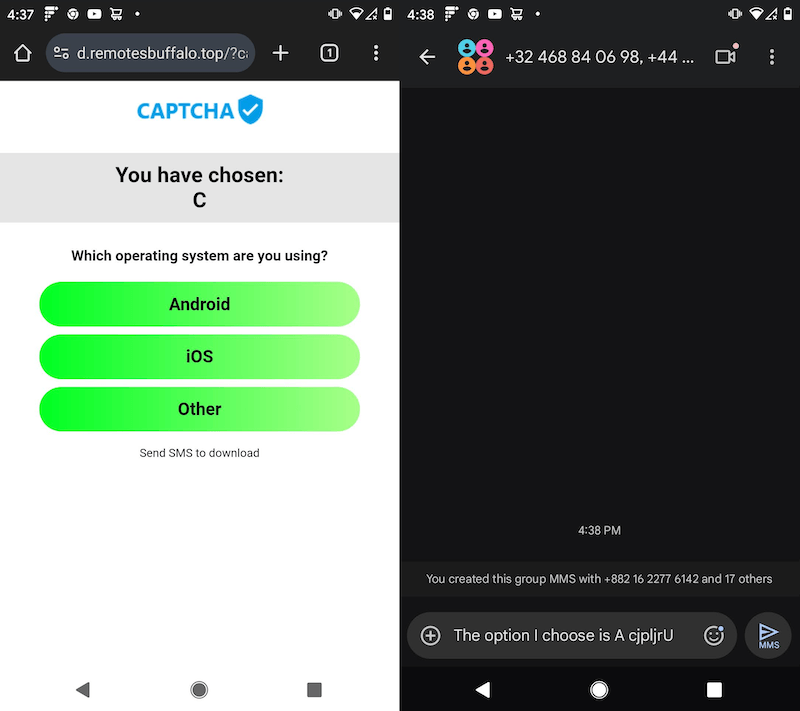
Figure 1. When a user encounters this IRSF actor, they will be taken through a series of fake CAPTCHAs, each requiring an SMS message to prove they are human. The images demonstrate a partial sequence of this experience. Source: Infoblox Threat Intel.
Traversing the TDS
When confronted with a fake CAPTCHA page, you might ask yourself, ‘How did I get here?’. The answer is, quite likely, a traffic distribution system (TDS). Our regular readers will think: of course!
In March 2026, we triggered this threat by visiting a lookalike domain to a major U.S. telecom company. From the lookalike domain, we were immediately redirected into a TDS (via colnsdital[.]com) and were then passed to hotnow[.]sweeffg[.]online, which we attribute with a high degree of confidence to a commercial TDS that is part of an affiliate advertising network based in Germany. From there, we were redirected to another TDS node, this one controlled by our SMS scam actor: zawsterris[.]com. In other words, the SMS scam actor is an advertising affiliate of the commercial TDS operator. We have not studied this affiliate network in-depth, and we do not know if they are aware of the affiliates using their network for this kind of fraud.
The next redirection was to the fake CAPTCHA page: d[.]ruelomamuy[.]com. After completing the CAPTCHA process, the TDS sent us to megaplaylive[.]com, another actor-controlled domain hosting gaming and video content that seems benign on the surface but is capable of continuing the scam. This redirect chain is shown in Figure 2, with the final three steps in red showing domains controlled by this SMS actor.
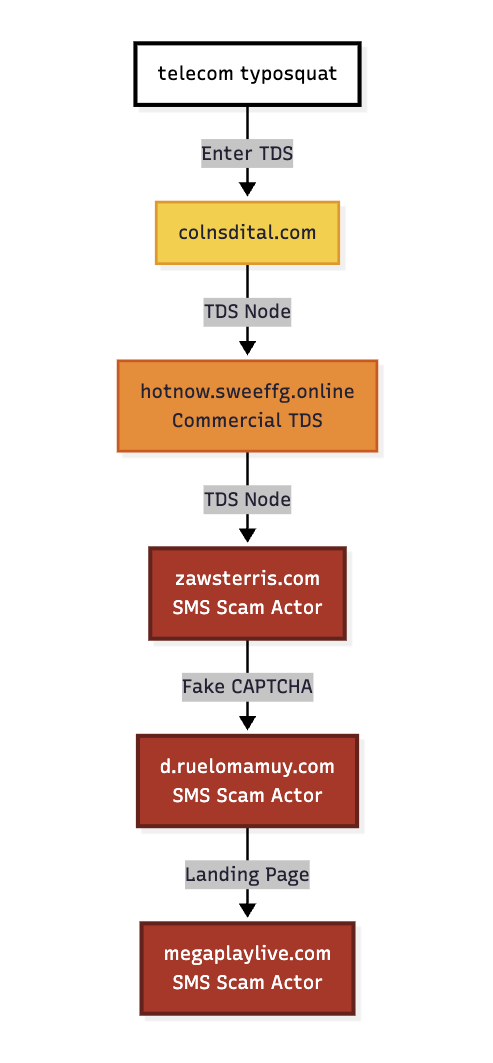
Figure 2. Initial observed redirection chain leading to fake a CAPTCHA page hosted on d[.]ruelomamuy[.]com
Several observations allowed us to associate the TDS node zawsterris[.]com to the SMS scam actor. The most notable one came through DNS: before hiding behind Cloudflare, zawsterris[.]com briefly resolved to an IP on AS15699 (Adam Ecotech), which is the same infrastructure we’d already linked to this SMS fraud campaign. Table 1 shows hosting and registration information for the domains used in this redirection chain.
| Domain | Function | IP ISP | Registrar | Attribution |
| <telecom typosquat> | Entry point | Digital Ocean | Media Elite | Unknown |
| colnsdital[.]com | TDS node | Hetzner | Namesilo | Unknown |
| hotnow[.]sweeffg[.]online | TDS node | Internap | GoDaddy | Commercial affiliate advertising network |
| zawsterris[.]com | TDS node | Cloudflare | GoDaddy | SMS scam actor |
| d[.]ruelomamuy[.]com | Landing Page | Cloudflare | GoDaddy | SMS scam actor |
| megaplaylive[.]com | Landing Page | Adam Ecotech | GoDaddy | SMS scam actor |
| Table 1. Domains used in the redirection chain | ||||
To monetize traffic in a TDS, tracking information needs to be passed along, and these details are typically put into the URL. Table 2 shows the parameters we observed during the commercial TDS stage of the redirection change, and Table 3 shows the parameters observed during the SMS scam portion.
| Campaign Parameter | Value |
| utm_medium | aa3e8d3009d94b9c89ac744b2be0687643493b0c |
| utm_campaign | sweeffg |
| Table 2. Commercial affiliate advertising network campaign parameters | |
| SMS Scam Parameter | Value |
| clientId | 254 |
| productId | 2001 |
| publisher_id | 23188&MU1FFF |
| af | 5002320649344840 |
| groupds | 166 |
| Table 3. SMS scam campaign parameters | |
The productId parameter was particularly interesting, as the value of 2001 appears both here and in the cookie analysis as a value in the list of “valid_products.” It implies that this landing page is one among many, and the campaign is much larger in scope than what we have observed.
Technical Overview
The fake CAPTCHA’s mechanics are straightforward but deceptive. It leverages social engineering by mimicking familiar verification tasks such as animal identification and text recognition, while hiding a crucial requirement: users must send an SMS message to proceed. This design funnels traffic to phone numbers distributed across 17 countries.
The CAPTCHA’s level of difficulty seems intentionally trivial. The fraud doesn’t depend on challenge complexity; it depends on SMS volume. Each of the multi-stage verification steps triggers a separate message to the server-designated numbers. The codebase handles both iOS and Android platforms through sophisticated server-side control, orchestrating each user action via command-and-control (C2) infrastructure. At a high level, the operation is as follows:
- User clicks any answer to a fake CAPTCHA question
- JavaScript calls makeTrackerDownload.php API endpoint
- Server returns phone numbers, SMS message, and control parameters
- JavaScript launches SMS app with pre-filled message and phone numbers
- After 5 seconds, JavaScript decides next action based on server instructions
When the victim submits an answer to the fake CAPTCHA, their phone launches their messaging app with a preconfigured message and destinations comprising the entire list of phone numbers. The user would then just have to hit send. With four steps of CAPTCHA, and 15 numbers identified in this attempt, 60 SMS messages in total are sent, maximizing the actor’s revenue across multiple countries and carriers.
There are four questions in the CAPTCHA process in step 1 above, which include asking for your device type (iOS or Android) and your network (3G, 4G, or WiFi). Each step triggers sending a message via SMS, which is prepopulated with the entire list of phone numbers received from the website. The DOM of the website also reveals the content of messages that are sent. Each message contains an {af}, for affiliate code, which is likely used to track the multiple campaigns that drive traffic to the site, and two contain {respuesta}, which is the answer for the question (“respuesta” is Spanish for response).
From the code:
- sms1 = “I want to continue {af}”
- sms2 = “The option I choose is {respuesta} {af}”
- sms3 = “The option I choose is {respuesta} {af}”
- sms4 = “Im not bot im real user {af}”
The control parameters mentioned in step 2 above allow dynamic updates to the operation to override default behavior. They include:
- “forceRedirectURL,” which could function as either a kill-switch or a redirection to drive traffic to another page
- “forceMessage,” which allows operators to change the SMS message without updating the HTML; this could be used to adapt to carrier filtering or language localization, among other possibilities
Back Button Hijacking
In addition to SMS-based social engineering, this campaign employs a dedicated back button hijacking mechanism to trap users on the fake CAPTCHA pages and increase the likelihood of SMS interaction. The dedicated JavaScript (see Figure 3), first observed in this campaign in January 2023, manipulates the user’s browser history using the pushState() method, effectively neutralizing the browser’s back button. When a user attempts to navigate away from the page via the back button, the script pushes the current page URL onto the history stack, logs the action to a server-side endpoint, and redirects the user back to the fake CAPTCHA page. This creates a navigation loop preventing the user from leaving the page without fully exiting the browser.
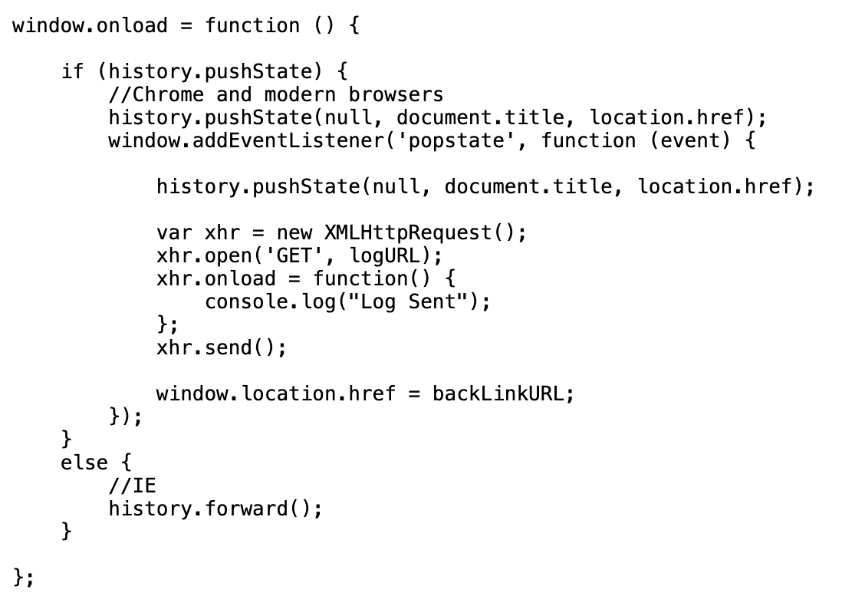
Figure 3. JavaScript for back button hijacking
Typically, the backlinkURL is the same as the URL the user is already on; however, in some cases, the value of the variable is set to a different URL hosting the same kind of scam page. Figure 4 shows an example for d[.]herbosfinx[.]com. If a user in this case were to hit the back button, they would be redirected to a new CAPTCHA hosted on d[.]santafebuno[.]top.
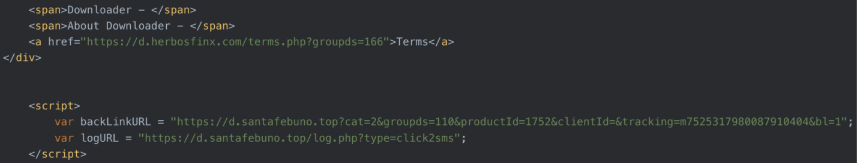
Figure 4. Code with backlink and log URL for d[.]herbosfinx[.]com. Source: urlscan.io
Terms of Service
The operators of the scam aren’t without their attempts at plausible deniability. At the bottom of the CAPTCHA pages is a form of legal fine print we often see with scams that attempt to deflect responsibility for the operation.
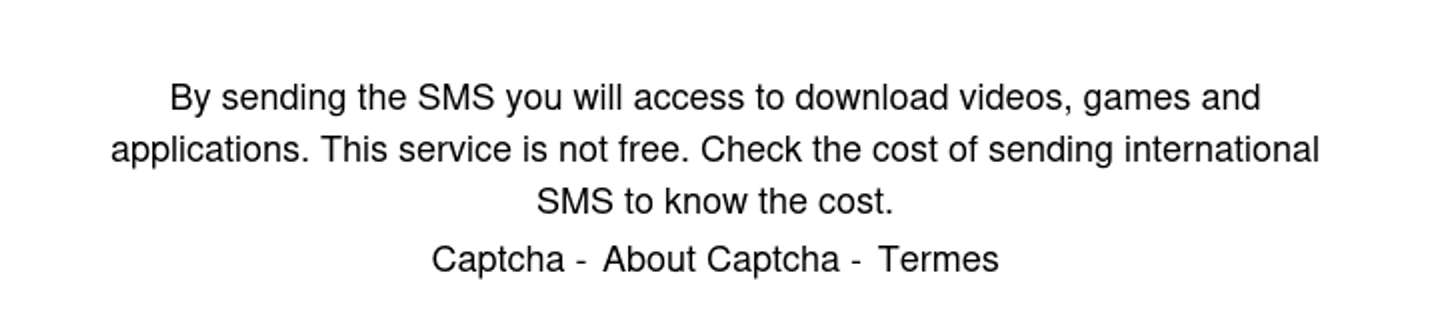
Figure 5. Text at the bottom of the CAPTCHA page
The disclaimer frames the CAPTCHA as a service exchange, then places the burden onto the victim to research pricing of international SMS. It does not state that there will be multiple SMS messages sent to over a dozen international destinations. The costs for the unreasonable number of SMS messages will be extraordinarily high due to the actor’s curation of the most expensive destinations to increase their return. This type of disclaimer is not a disclosure: it’s misdirection from the fact that the entire CAPTCHA process is fake.
Phone Number Analysis
The website’s DOM reveals how to retrieve the phone numbers used to drive the scam. Using a GET request observed in the code, we can craft a simple curl command to query the server and retrieve the phone numbers. Additionally, nested in the response is a key, “urlContent,” which contains the destination to redirect the victim to, bundled with a base64 string within the URL. In our example, the decoded string contains 20 additional phone numbers, which after the completion of the CAPTCHA process, were passed within the redirection to the megaplaylive[.]com domain.
Example curl command (safelinked, complete numbers redacted):
curl -s ‘https://d[.]ruelomamuy[.]com/makeTrackerDownload.php?a=WEBSMS&s=5002320649344849&c=US&groupds=138&caf=5002320649344849&origSms=I%20want%20to%20continue%205002320649344849&step=9’ | jq .
Response (safelinked):
{
“phoneNumbers”: “+9947764824XX;+31970391393XX;+31970391383XX;+4473560342XX;+2652229761XX;+324802180XX;+337576670XX;+417846132XX;+9592636943XX;+316352451XX;+324640995XX;+3937803063XX;+487802079XX;+9051026608XX;+347007503XX”,
“os”: null,
“urlContent”: “http://megaplaylive[.]com/?enc=eyJwaG9uZU51bWJlcnMiOlsiKzIwMTAwNTc5NzQ1MiIsIisyMDEwMDQ5MzkxNzgiLCIrMjAxMDA1Nzk2Mzg5IiwiKzIwMTAwNDk1MTYyNiIsIisyMDEwMDU4MDMzNzkiLCIrMjAxMDA2MzQ4ODc5IiwiKzIwMTAwNDkzOTE0NSIsIisyMDEwMDUyMDk2NzYiLCIrMjAxMDA2MzQzOTk3IiwiKzIwMTAwNjM1MzY5MyIsIisyMDEwMDk0MDg1ODQiLCIrMjAxMDA1Nzk2Mzk5IiwiKzM4MDkyNzg4NTQ2MiIsIiszODA5MjI0MTg0MDQiLCIrNDQ3NDkwOTIwODEwIiwiKzQ2NzY2NzQ2NDUxIiwiKzQzNjcwMzA2ODEwNyIsIis3NzkwNTAwMDIyNSIsIiszMjQ2NzQ0MDQyNyIsIis0NDc4NDg1MDk0NDgiXSwiYWYiOiI1MDAyMzIwNjQ5MzQ0ODQ5IiwiZGV2IjpudWxsLCJ0eXBlIjoiZ2FtZXMiLCJsYW5nIjoiZW4iLCJsb2FkZXIiOmZhbHNlLCJjaWQiOm51bGwsInBpZCI6bnVsbH0=”,
“codeAF”: “lfzmfSzw”
}
From these commands we have two tiers of phone number lists. One is used in the CAPTCHA scheme (see Table 4), and the other is passed onwards to the ‘game’ site megaplaylive[.]com (Table 5).
The phone numbers illustrate a global range of SMS destinations, spanning seventeen countries, including many locations known for having higher than average termination fees, such as the Netherlands, Myanmar, and Azerbaijan.
15 Tier 1 Phone Numbers (from a single fake CAPTCHA)
| Number | Country | Code |
| 9947764824XX | Azerbaijan | +994 |
| 31970391393XX | Netherlands | +31 |
| 31970391383XX | Netherlands | +31 |
| 4473560342XX | UK | +44 |
| 2652229761XX | Malawi | +265 |
| 324802180XX | Belgium | +32 |
| 337576670XX | France | +33 |
| 417846132XX | Switzerland | +41 |
| 9592636943XX | Myanmar | +95 |
| 316352451XX | Netherlands | +31 |
| 324640995XX | Belgium | +32 |
| 3937803063XX | Italy | +39 |
| 487802079XX | Poland | +48 |
| 9051026608XX | Turkey | +90 |
| 347007503XX | Spain | +34 |
| Table 4. List of phone numbers used in CAPTCHA scheme | ||
20 Tier 2 Phone Numbers (passed to megaplaylive[.]com)
| Number | Country | Code |
| 2010057974XX | Egypt | +20 |
| 2010049391XX | Egypt | +20 |
| 2010057963XX | Egypt | +20 |
| 2010049516XX | Egypt | +20 |
| 2010058033XX | Egypt | +20 |
| 2010063488XX | Egypt | +20 |
| 2010049391XX | Egypt | +20 |
| 2010052096XX | Egypt | +20 |
| 2010063439XX | Egypt | +20 |
| 2010063536XX | Egypt | +20 |
| 2010094085XX | Egypt | +20 |
| 2010057963XX | Egypt | +20 |
| 3809278854XX | Ukraine | +380 |
| 3809224184XX | Ukraine | +380 |
| 4474909208XX | UK | +44 |
| 467667464XX | Sweden | +46 |
| 4367030681XX | Austria | +43 |
| 779050002XX | Kazakhstan | +7 |
| 324674404XX | Belgium | +32 |
| 4478485094XX | UK | +44 |
| Table 5. Phone numbers used passed to game site | ||
After completing the fake CAPTCHA, the victim is redirected to megaplaylive[.]com, which seems to only exist for the purpose of this operation, and like many of the domains mentioned in this article, is hosted on AS15699 (Adam EcoTech). As demonstrated with URLScan, the page cannot be accessed directly by visiting the second-level domain (SLD) megaplaylive[.]com. We observed an example of the fake CAPTCHA process leading to megaplaylive[.]com on the online sandbox tool ANY.RUN.
It wasn’t until we researched the domain thoroughly that we uncovered the ‘contentType’ parameter, which when set to ‘sexy’ revealed the continuation of the SMS scam. With the correct settings, we could access a page where the code demonstrated how each click of ‘play’ on an adult video would launch another SMS message configured with 20 international recipients. The ‘sexy’ (their word) version of megaplaylive loads JavaScript that controls this portion of the operation.
DNS Patterns
The actor hosts the fake CAPTCHA pages in this campaign on both SLDs and various subdomains of these SLDs. SLDs can vary but most follow one of two patterns shown in Table 6. Subdomains include cd, chat, click, d, r, raffles, v, vids, etc., with d and r used most frequently.
| Domain Pattern | Examples |
| RDGA-generated domains featuring repeated words/strings (typically used in two or three domains) mixed with other random words or characters | panzozerrot[.]com / zerrotmamil[.]com remotesbuffalo[.]top / buffalosolpe[.]top vistertransit[.]com / transitcaxip[.]com fufecarrol[.]top / carrolvassin[.]top |
| Domains/subdomains featuring content themes, e.g., win, chat, tips, vids. | vids[.]chatorizon[.]com chat[.]matchnewtoday[.]com claimandwins[.]com 4lifetips[.]com |
| Table 6. Domain patterns used in CAPTCHA campaign | |
DNS analysis shows most domains and subdomains used in this campaign have consistently resolved to a small set of dedicated IP addresses on an ASN based in Spain (AS15699 Adam EcoTech, S.A.) since the first observed CAPTCHA page in June 2020.
Domains are registered using NameSilo or GoDaddy and use DNS Made Easy (DME) and DigiCert nameservers. Some domains following the web content theme (chat, tips, giveaway, etc.) have been seen using dedicated name servers.
During this investigation, we repeatedly observed references to an affiliate advertising network based in Europe. We have not studied this company in-depth, and we do not know if they are aware of the use of their network for IRSF fraud. The company’s website claims they are “the greatest company for Click2SMS” and that they offer carrier billing with “all kinds of traffic allowed.” Click2SMS is an affiliate marketing model that generates revenue through carrier billing by prompting mobile users to send an SMS message to a designated number(s) through a single click. Based on the name servers and other technical supporting information, we are confident that the threat actor we observed is an affiliate of this Click2SMS network.
Mentions of the company name and Click2SMS can be seen in website code, in registration and hosting information for some of the domains, and even in dedicated cookies these domains use for tracking. The company’s origins are also similar to many other elements in this campaign, including the language of the code, as well as the IP space used to host the CAPTCHA pages and the nameservers of the gaming/adult content domains.
The company was referenced in the megaplaylive[.]com website code related to the push notification service it employs. For years, Infoblox Threat Intel has reported on cases where actors use push notifications to establish persistence on a victim’s device, and that is again likely the case here. If a victim were to allow push notifications, the operator of the service would gain the ability to drive notifications to the device, directing the victim to return to the site for new content, or send them elsewhere to other scams.
Cookie Analysis
Similar to other adtech and TDS operations, this campaign relies heavily on browser cookies to track user and campaign attributes, as well as dynamically control traffic flow. These cookies store contextual information such as user geolocation, language, internet service provider (ISP), etc. Additional cookie values track progression through the multi-stage verification flow, enforce step limits, and even set a rate of probable success of the campaign, allowing operators to filter non-optimal users. The fake CAPTCHA pages have set the same three to four seemingly dedicated tracking cookies since the beginning of this campaign in June 2020, including cookies mentioning tracking and c2s, likely referring to Click2SMS. Table 7 below shows an example of one of the decoded cookie values.
Table 7. Decoded cookie value set by d[.]marraheltin[.]com
We observed the success rate value stored in the cookie value being actively used by the fake CAPTCHA page’s client‑side code to determine the user’s next action based on their suitability for the campaign, as shown in Figure 6.
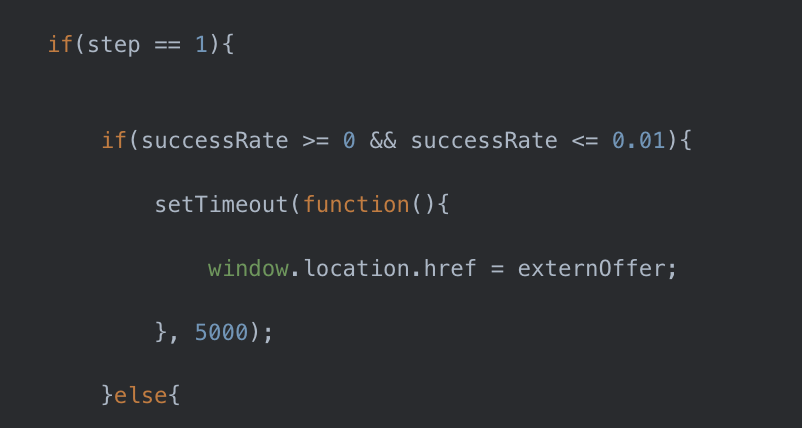
Figure 6. Code used to redirect non-targeted users to other fake CAPTCHA pages
When the user is on the first step of the CAPTCHA flow, the code evaluates a pre-calculated successRate value stored in the cookie containing data on the user. If the user is deemed a non-ideal candidate for the campaign, the page redirects them to an alternate URL defined by the externOffer variable, which points to a new fake CAPTCHA page. The differences in hosting and registration patterns of the SLDs set in the externOffer variables, along with stylistic differences in the CAPTCHA pages, indicate these may be part of a separate campaign or controlled by a different actor. Figure 7 shows an example of these new pages impersonating Lush, a legitimate cosmetics company (don’t miss the time-pressure tactic: don’t let robots claim the bath bomb—complete the form!). The externOffer value for this page is set to:
hXXps://verifysuper[.]com/cl/i/wopmej?aff_sub4=5002320649344849&aff_sub5=US
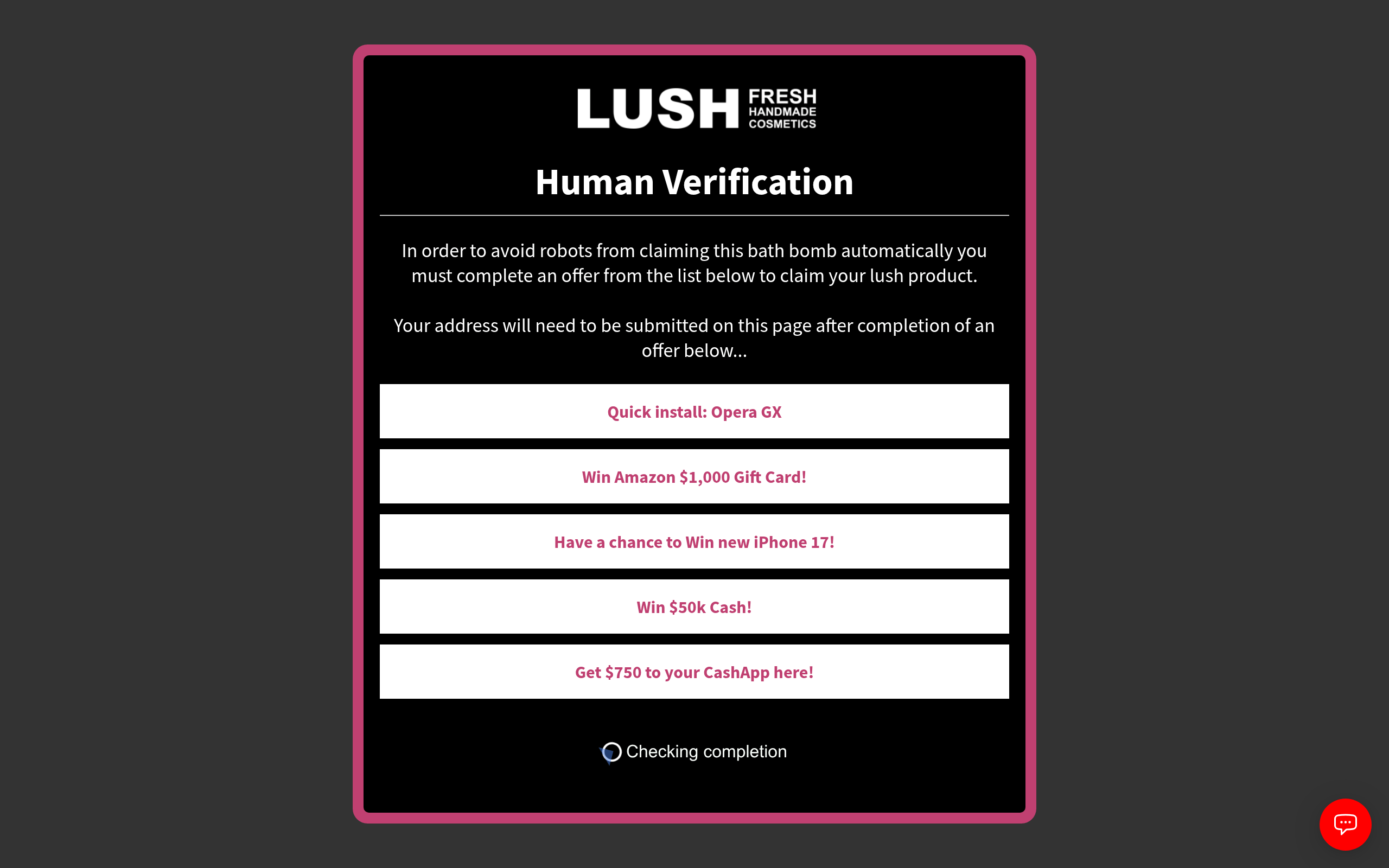
Figure 7. externOffer fake CAPTCHA page impersonating Lush Cosmetics and hosted on verifysuper[.]com. Source: urlscan.io
SMS: Another Drop in the Scam Bucket
This research represents one operation we were able to thoroughly document; however, the history of the domains, the application of affiliate codes, and international telecom and TDS infrastructure suggest that it is not unique, but rather part of a broader ecosystem. Visiting a typosquat domain of a major telecom brand is what originally initiated this investigation, and that led us to an international revenue sharing fraud scheme that seems to have gone underreported for years—one that creates victims of both individuals and telecoms. Our findings here add to our years of research showing that the malicious use of TDSs is one of the most significant threats on the internet today, and brings attention to a new lesson: avoiding pop-ups, spoofed pages, and compromised sites isn’t enough to stay safe: don’t send texts to confirm you are human either.
Indicators
A curated selection of indicators related to the threats discussed can be seen in the table below. A more comprehensive list of indicators can be found in our GitHub repository.
Note: Some domains/hostnames listed below may no longer be active or used in this campaign.
| Indicators | Description |
| colnsdital[.]com | TDS domain leading to fake CAPTCHA page |
| hotnow[.]sweeffg[.]online | Commercial TDS hostname |
| zawsterris[.]com | SMS-actor controlled TDS domain |
| megaplaylive[.]com chat[.]matchnewtoday[.]com vids[.]chatorizon[.]com |
SMS actor-controlled domains hosting fake gaming, chat, and video content |
| d[.]fufecarrol[.]top d[.]herbosfinx[.]com d[.]marraheltin[.]com d[.]panzozerrot[.]com d[.]remotesbuffalo[.]top d[.]ruelomamuy[.]com d[.]santafebuno[.]top d[.]vistertransit[.]com d[.]zerrotmamil[.]com r[.]buffalosolpe[.]top r[.]carrolvassin[.]top r[.]transitcaxip[.]com |
SMS actor-controlled domains actively hosting fake CAPTCHA pages |
| claimandwins[.]com 4lifetips[.]com | Domains hosting older versions of the fake CAPTCHA/download pages |
| verifysuper[.]com | externOffer domain hosting fake CAPTCHA pages |








