Authors: Infoblox Threat Intel and Confiant
Executive Summary
Recently we published the first part of a four-month-long study conducted with Confiant on the abuse of Keitaro, an advertising performance tracker frequently abused by threat actors. We ran out of pages before we ran out of examples. The first blog focused on the use of AI, particularly in investment scams, and barely scratched the surface of how Keitaro is abused. This installment demonstrates how a broad spectrum of threat actors abuse commercial, feature-rich, easy-to-use tools like Keitaro to reach victims. In the modern, mass-scale criminal economy, risk is highly dependent on reach.
| Disruptive technology should be framed as a marketing challenge, not a technological one. — Clayton M. Christensen |
Christensen’s observation explains why even the most technically proficient malware operators have embraced adtech: breakthrough tooling is inert without distribution. In campaigns where Keitaro is used, this all-in-one adtech (tracker, traffic distribution system, and cloaker) functions as the logistics that converts capability into impact. It finds real people, in real time, whose environments are compatible with the payloads on offer. After all, threat actors are not a threat if they can’t find victims that are compatible with their products (i.e. threats).
Commercial adtech lowers the barrier for threat actors by outsourcing part of the delivery mechanism. Instead of building and maintaining their own routing, profiling, and targeting stacks, operators can focus on crafting (and constantly iterating) malicious campaigns while the platform optimizes who sees what, and when. Distribution is the decisive edge; without it, the most advanced malware is little more than a lab demo.
The majority of observed Keitaro instances are operated by actors with ties to Eastern Europe, frequently fronted by Cloudflare or hosted in bulletproof providers. These configurations frustrate attribution and slow down disruption efforts from the security community. Although investment scams dominate the use of Keitaro in our study, other activity includes:
- Malware delivery pipelines (loaders, infostealers, and weaponized remote administration tools)
- Crypto theft operations (wallet drainers targeting NFT owners)
- Spam‑to‑phish/eCrime funnels where email campaigns resolve to Keitaro gates before redirecting to phishing kits or employment scams
- Domain‑centric social deception, including lookalike domain farms and RDGA (registered DGA) patterns that keep lures fresh and reputations clean
- Gambling geo‑gates that selectively expose betting sites by location
- Domain hijacking techniques that exploit DNS lame delegation, aka the Sitting Ducks vulnerability
- Fake online pharmaceuticals, investment schemes, and malicious adtech (fraud via push notifications)
A few of the highlights we cover in this segment:
- Over 20% of the threat actors tracked by Confiant during this period used Keitaro, with some obtaining tens of millions of impressions
- 96% of spam campaigns that included links to Keitaro instances led to cryptocurrency wallet drainers in a hybrid scam and phishing attack
- Our use of JA4+ techniques to identify malware download sites, particularly ones hosted in bulletproof provider AS214351
- The use of fake arrests as clickbait lures leading to investment scams
- Spam campaigns generating localized, dynamically crafted messages disguised as employment-related salary notifications
- Reward scam campaigns targeting Brazilians to gain PII, specifically Cadastro de Pessoas Físicas (CPF) Numbers (individual taxpayer ID), Pix Key (instant payment identifier such as phone, email, CPF or unique key), and CNH (driver’s license number)
Keitaro’s popularity among threat actors raises a simple question: why does it keep winning mindshare? The answer comes down to the economics of consolidation and a product whose features they can leverage. In many malicious adtech stacks, operators pay separately for a tracker, a cloaker, and a traffic distribution system (TDS). Keitaro bundles all three, reducing cost and operational friction while providing a single console for analytics, routing policies, and rapid iteration. This consolidation lowers the barrier to entry, shortens setup time, and makes scaling campaigns significantly easier. It is also easy to use and available in major hosting providers.
Unfortunately, while we found Keitaro’s owners, Apliteni, both receptive and responsive to abuse reporting, the volume of threat domains is more than we can realistically gather evidence for them to action. In addition, stolen licenses are widely used, particularly by the more sophisticated criminals. We’ll cover more of the Keitaro technology and the challenges with large-scale abuse reporting in the final segment of this series.
Ultimately, Keitaro is just one of many tools used in the cybercriminal ecosystem, but the feature set has made it attractive to malicious actors who want to maximize their victim reach with the least effort.
Confiant secures the digital advertising supply chain and protects many major advertising exchanges, platforms, and publishers. Their visibility of close to 90 billion ad impressions a month on publisher sites is derived from thousands of client-side integrations that block malvertising attacks. This product suite also collects on threat activity seen in the wild and serves to complement the view Infoblox Threat Intel has via DNS, spam, and website scans.
Threats By the Numbers
Keitaro‑enabled campaigns distribute a wide variety of threat types: scams, phishing pages, malware distribution, and more (see Figure 1). In the sections that follow, we examine the most prominent threat types observed in our data and highlight representative examples of how threat actors are leveraging Keitaro across these different use cases.

Figure 1. Relative distribution of content types observed using Keitaro
Spam Campaigns
Among threat actors abusing Keitaro, we identified 25 who were using spam as an initial attack vector to distribute malicious content. In aggregate, these actors conducted approximately 120 campaigns and sent tens of thousands of emails during the four-month period. The campaigns primarily pushed cryptocurrency and non-fungible token (NFT) airdrop scams, banking credential phishing, ClickFix‑based malware delivery, and romance/investment fraud. Wallet drainers were by far the biggest campaigns we observed in spam-related activities. Approximately 96% of spam emails delivered scams that lured victims into approving fraudulent cryptocurrency transactions for the purpose of wallet draining (see Figure 2).
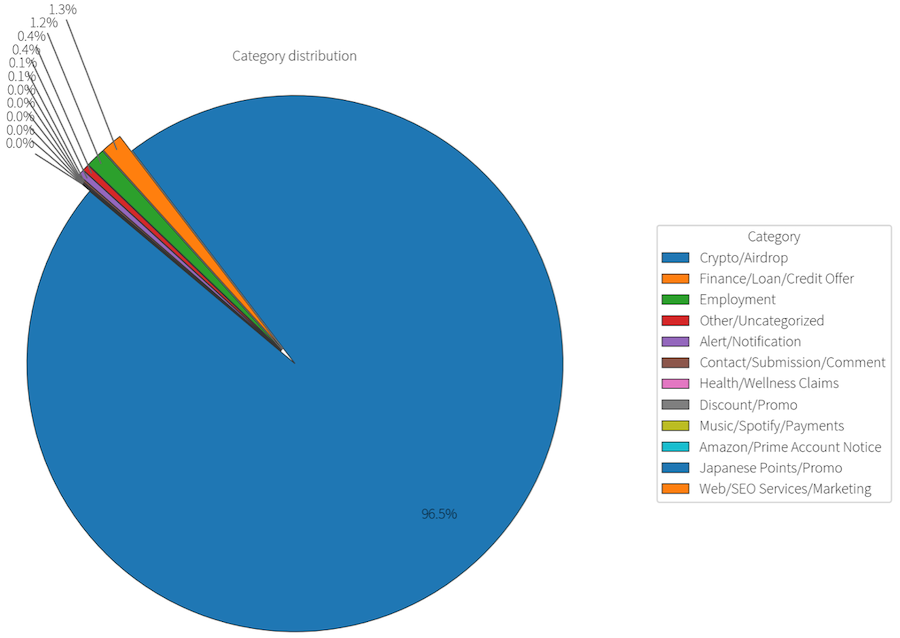
Figure 2. Distribution of observed spam campaigns utilizing Keitaro
We tokenized the subject line of each spam email and used those tokens to derive labels commonly seen in spam campaigns that routed traffic through Keitaro. We then analyzed each token set to estimate the core theme of the message and grouped the dataset into 12 categories. In Figure 3, we selected the top three tokens per category and rendered a heat map to compare themes at a glance. This view helped us see the range of social engineering lures and how they concentrate across categories in a single, simple view. The links redirected victims to websites that used Keitaro to track or conditionally redirect to other malicious landing pages.
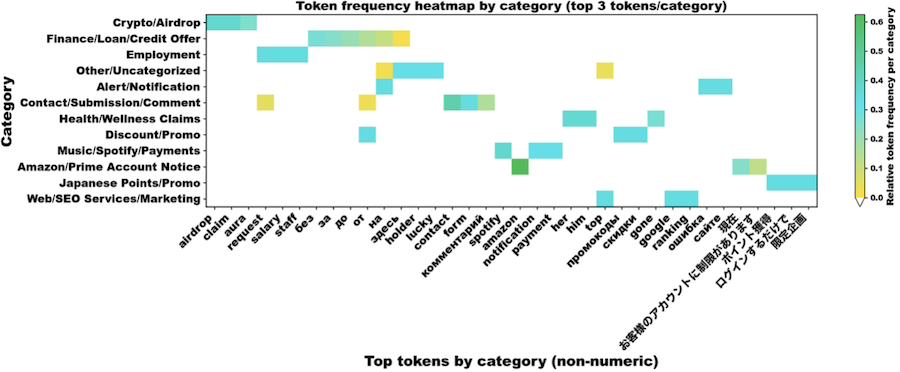
Figure 3. Popular token labels by spam category
Malvertising
On average, Confiant tracks around 30 active malvertising threat actors with high-confidence attribution over a typical 90-day period. Over the date range in scope for the findings in this report, eight of these threat actors have been identified as leveraging Keitaro for cloaking or traffic distribution. Substantial activity was also observed among a multitude of malicious campaigns that are not currently attributed to any known actor clusters but that did use Keitaro for cloaking. Among the dataset, some campaigns ran at such prodigious volumes that tens of millions of impressions were observed client-side associated with these unattributed, lone-wolf IOCs.
Threat Highlights
To show the breadth of threats seen in the wild, we’ll showcase examples of:
- Malware
- Phishing
- Scams
- Illegal content (often these are really scams)
Malware
JA4+ Fingerprinting Uncovers Keitaro Servers Used for Malware Delivery
The JA4+ network fingerprinting suite allowed us to identify web servers that expose the Keitaro admin console, complementing our other data sources. The admin portal is the self‑hosted web UI for the Keitaro Tracker. It’s where operators configure campaigns, flows, landing pages, offers, traffic sources, and domains; view reports; and manage integrations and access (see Figure 4). This methodology produced over 100 IP addresses that were associated with malware distribution and appeared largely unreported in public threat intel sources at the time of collection.
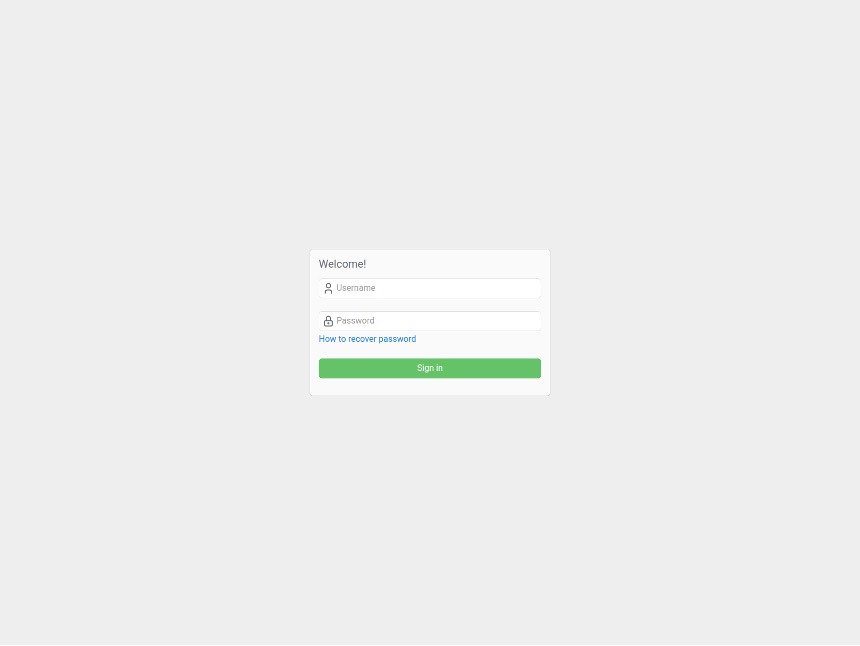
Figure 4. Keitaro’s web UI admin login page
Among the Keitaro IP addresses that we identified, the most notable was a subset managed by ISP FEMO IT SOLUTIONS LIMITED (AS214351). This organization registered with the RIPE NCC on August 15, 2024, and is less than two years old. It only operates 3 /24 prefixes and has been described in open-source reporting as a bulletproof hosting services provider. Its upstream provider is aurologic GmbH. Open‑source reporting has described aurologic as a central nexus within the malicious infrastructure ecosystem and, in Insikt Group analysis, identified networks such as Virtualine Technologies, Femo IT Solutions Limited, Global-Data System IT Corporation (SWISSNETWORK02), Railnet, and the recently sanctioned Aeza Group among threat‑activity enablers (TAEs). Figure 5 shows the various malware samples analyzed in Joe Sandbox and distributed via AS214351.
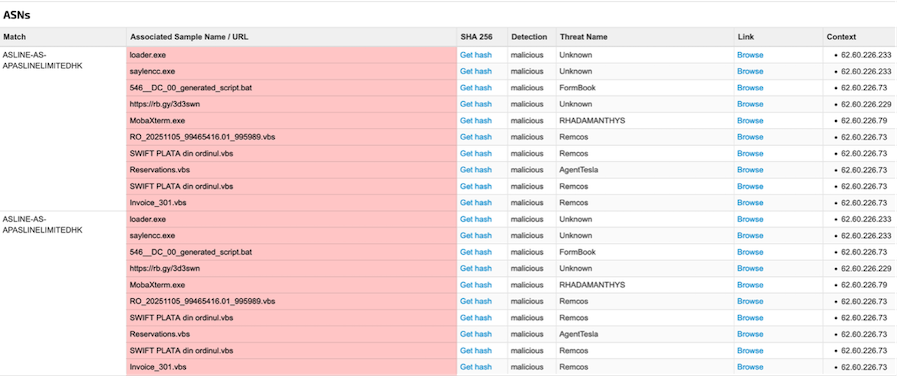
Figure 5. Malware payloads hosted on AS214351
Many of the Keitaro IP addresses we saw in the AS214351 network host and distribute malware. For instance, in November and December 2025, 62[.]60[.]226[.]248 hosted the DonutLoader malware payload (SHA256: b98b53ca03e3e9009b31bcc37b90b206064b25effce449dde63c51cef6a47470), a memory‑only loader that turns PE/.NET/DLL/script into shellcode and injects them into other processes. In the attack that we observed, the DonutLoader injected the StealC v2 information stealer into Chrome and Microsoft Edge browser processes. The malware targeted multiple categories of sensitive information:
- Browser Data: Harvests cookies, login credentials, and browsing history from Chrome and Edge browsers by accessing their respective data files
- Cryptocurrency Wallets: Attempts to steal wallet files from multiple cryptocurrency applications including Electrum, ElectronCash, Daedalus Mainnet, and WalletWasabi
The malware’s C2 configuration (see Figure 6) showed that StealC sends stolen data to hXXp[:]//62[.]60[.]178[.]163/ce369e7324834845[.]php. The configuration contained a “Botnet” tag used by the operator and the panel to group victims, pivot IOCs, and apply rules (e.g., geofencing, payload rules). It also contained the “Traffic RC4 key” for network encryption of StealC v2’s protocol (request/response payloads), as well as the “Rc4 Key” for decrypting strings, API names, and configuration details. According to network fingerprinting databases, 62[.]60[.]226[.]248 exposed a Keitaro admin login console (Keitaro local version: 11.0.19) in November and December 2025 and continues to do so as of this writing.
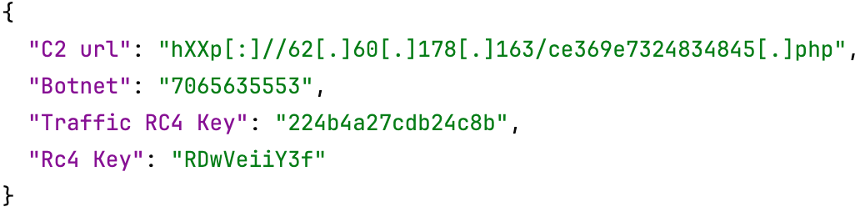
Figure 6. StealC v2 C2 configuration
During summer 2025, 62[.]60[.]226[.]248 was also hosting a customized remote monitoring and management (RMM) client called ScreenConnect that auto-enrolled victims into the actor-controlled network relays. Figure 7 shows the standard ScreenConnect (ConnectWise Control) web portal that was accessible via hXXps[:]//object[.]brovanti[.]com/. This website was hosted on 62[.]60[.]226[.]248 in August 2025. Adversaries that use RMM TTPs commonly stand up their own ScreenConnect server and then distribute pre‑configured access‑agent installers so victims auto‑enroll into that instance. The same host (i.e., IP address) typically serves the portal UI, relay service, and installer downloads, so seeing both the customized binary and the portal on the same IP address is expected. The follow-on malware after the ScreenConnect installation was RustyStealer, an information stealer that functions as a credential-harvesting tool and delivers other malware. Open‑source reporting indicates that RustyStealer activity has been observed preceding Ymir ransomware deployment in some intrusion chains.
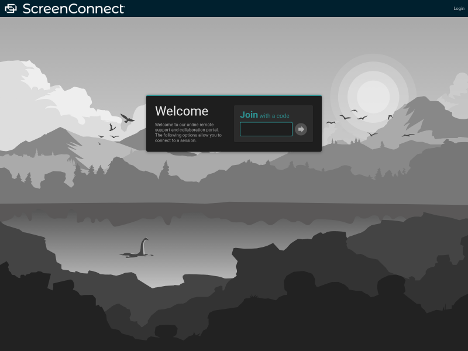
Figure 7. Example of an attacker-controlled ScreenConnect control web portal served by object[.]brovanti[.]com
Phishing
Phishing malvertising chains usually fall into two categories: credential theft and PII harvesting. Credential theft includes masquerading as an established web portal where victims attempt to log in, and their account details are siphoned off by the attacker. This is more common in search ads, where malvertisers take advantage of victims’ intent (based on their search keywords) to log into a system.
PII harvesting on the other hand is the favorite monetization path for criminals operating via display ads. The subterfuge involves giveaway scams like the “You’ve won an iPhone” or “Spin the wheel to win” money pages. Victims are lured to fill out a bunch of forms to claim their prize and may be required to give up information like their name, email address, phone number, or even credit card number.
TilapiaParabens
TilapiaParabens is a ‘rewards scam’ phishing campaign targeted at Brazilian audiences with deceptive short-format mobile video ads (TikTok style). Confiant has been tracking them since March 2025. It leverages high domain churn, consistently spinning up multiple new campaigns and domains daily over extended periods.
The abuse is identity and PII theft—specifically Cadastro de Pessoas Físicas (CPF) Numbers (individual taxpayer ID), Pix Key (instant payment identifier such as phone, email, CPF or unique key), CNH (driver’s license number), etc.
They typically use local cloaking kits such as The White Rabbit and Cloakilio, but the dataset that was in scope for this report showed multiple instances of Keitaro used for cloaking as well. These kits cloak landing pages that are paired loosely with the content that matches their domains (e.g., Figure 8). The money page takes victims through giveaway scams where they’re warmed up with a questionnaire (seen in Figure 9). Ultimately, victims are tricked into giving up their information for the bogus reward claim on PII harvesting pages similar to Figure 10.

Figure 8. TilapiaParabens scam landing page sample
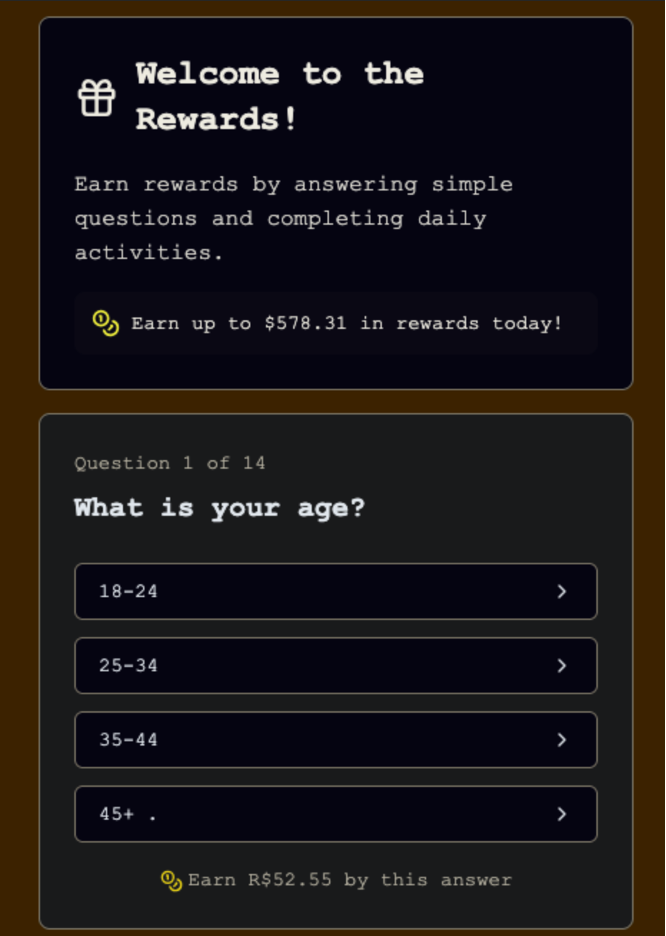
Figure 9. TilapiaParabens warm-up quiz sample from a previously uncloaked campaign
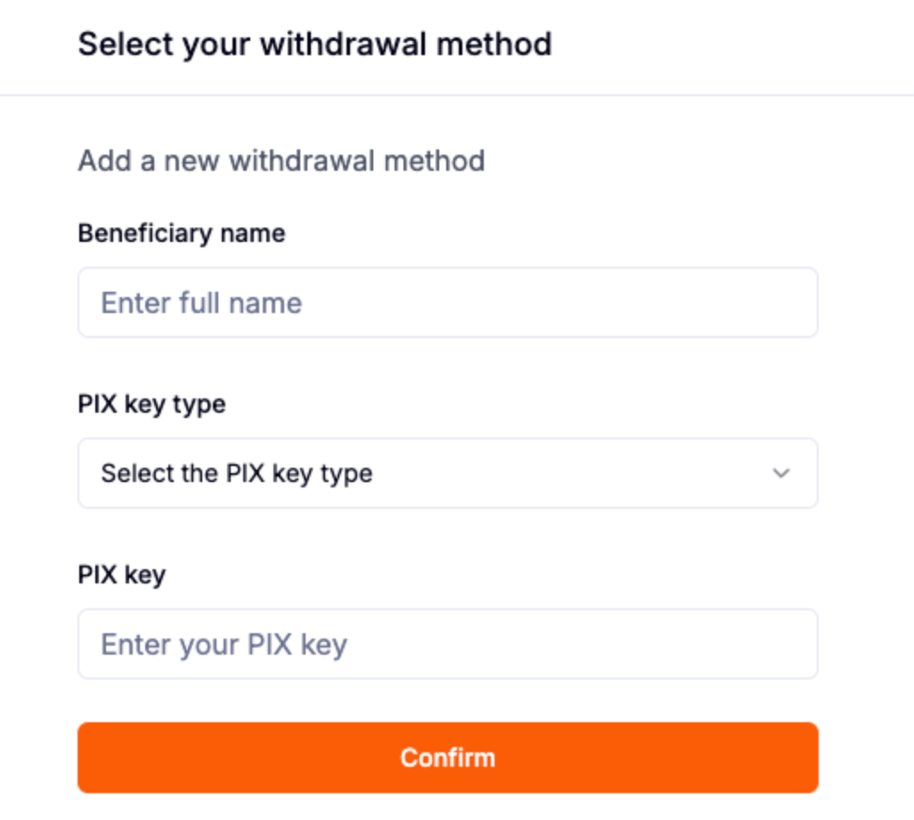
Figure 10. TilapiaParabens PII harvesting sample
Spam Campaigns
From October 2025 through January 2026, we observed multiple phishing campaigns impersonating popular services such as Netflix and Spotify. Each campaign relied on the same lure: a fabricated alert claiming the victim’s payment method had failed. The actors employed a security evasion technique known as hash‑busting, which involves adding or mutating low-value content so that each email produces a unique hash.
Figure 11 shows how one actor added personalized content, including crude or taunting remarks directed at security professionals, inside parts of the HTML that are not rendered. In this case, the actor placed both a random MD5‑like token and the hostile commentary inside HTML comments within the message body. Although the recipient never sees this content, it ensures that the HTML hash or fuzzy hash differs across messages, reducing the effectiveness of simple signature‑based anti‑spam rules.
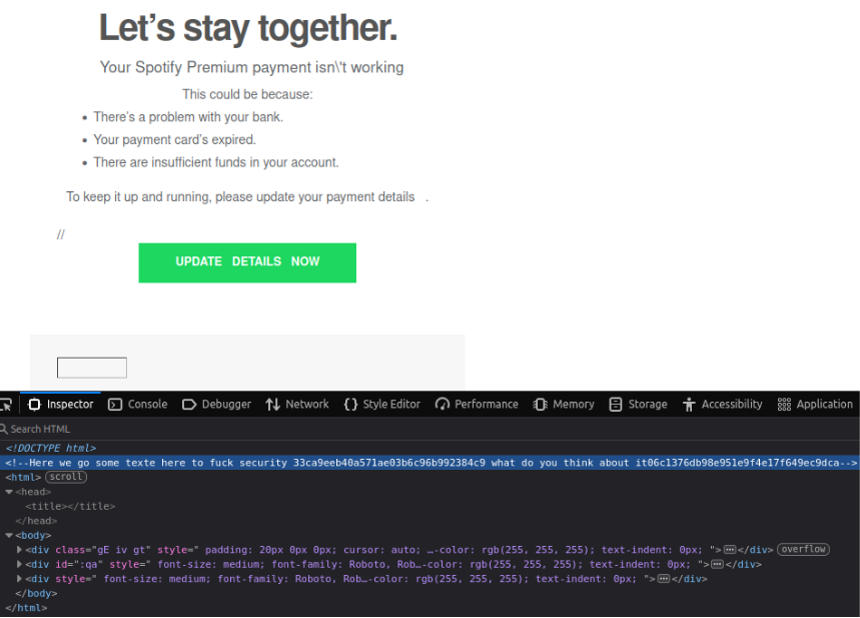
Figure 11. Hash-busting technique used in a phishing email attack; the update button is hyperlinked to hXXps[:]//membros[.]mtcreatingimages[.]com/spotify
Localized Attacks
We identified spammers generating localized, dynamically crafted messages disguised as employment-related salary notifications. Mail Transfer Agent transaction data showed that the attacker spoofed business email accounts and tailored messages to specific phishing targets. Figure 12 illustrates one case involving the spoofed account admin[@]jjim[.]co[.]kr; the email domain has been parked since its creation. The attacker used this address to deliver emails containing an embedded link: hXXps[:]//estrategicadesenvolvimento[.]com[.]br/Webmail/webmail[.]php?email={victim@email}
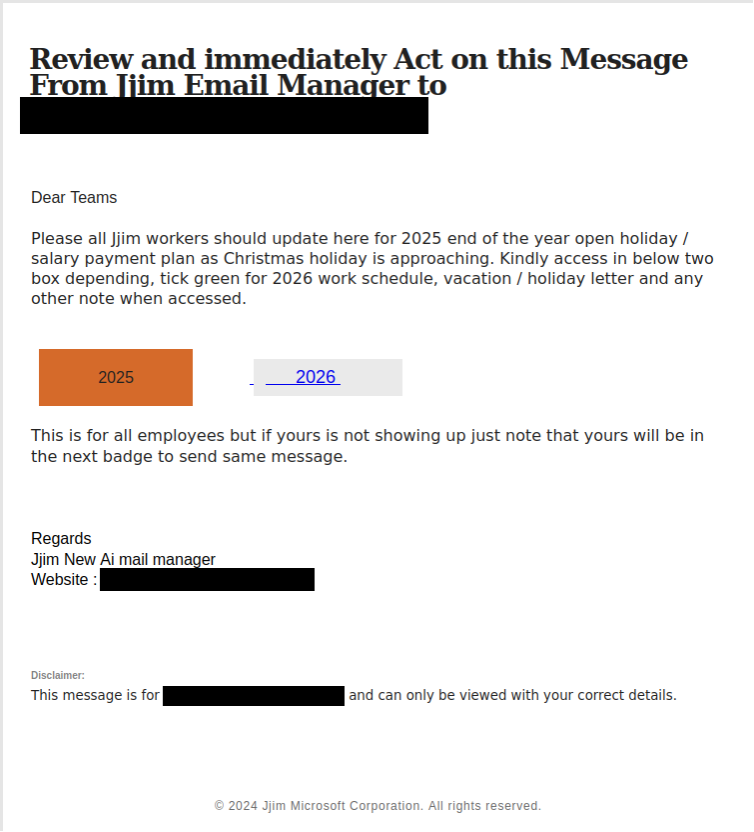
Figure 12. Dynamically crafted phishing email impersonating a corporate email system, localized for target
The associated mail server IP address (158[.]94[.]209[.]29) has known ties to Remcos RAT malware command-and-control (C2) infrastructure. When victims clicked the link, they were redirected to a fraudulent webmail login page, pre-populated with their own email address in the username field (see Figure 13).

Figure 13. Phishing page pre-filled with username
Unnamed Lookalike Actor
We have been tracking an unnamed actor running a phishing campaign impersonating Canadian financial institutions and other high‑trust service providers. The earliest creation date for domains we’ve attributed to this actor is February 2025, and they are still actively creating domains as of March 2026. The actor registers domains infrequently, creating them only on scattered days and in very small numbers rather than at a consistent pace. This irregular, low‑volume activity suggests they may be trying to stay under the radar and avoid detection.
The actor creates lookalike domains that mimic targets such as Canadian enterprises and organizations, including all the major banks and many other important organizations. In parallel, they also spoof the branding of shipping and logistics companies (DHL, FedEx, Canada Post) as well as government and retail services such as Costco. These domains host phishing pages featuring login portals, package‑tracking pages, refund notifications, and authentication pages. The screenshots in Figure 14 show examples of content for the domains rbcsecurityservices[.]com and interac-gigadat15[.]info.
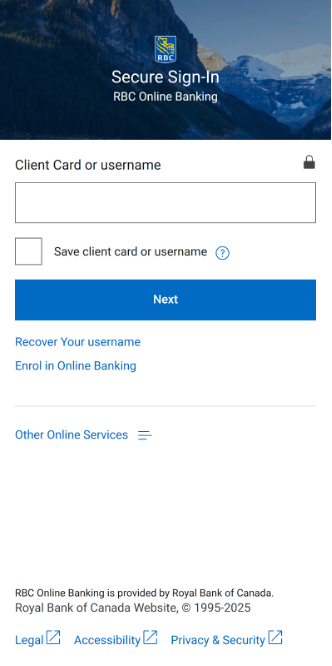
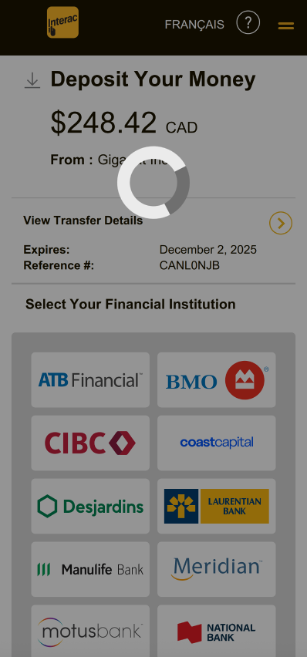
Figure 14. Landing pages for lookalike domains impersonating Canadian financial institutions. Image credit: urlscan.io
The actor’s operational pattern suggests automated or scripted domain creation: registrations appear in clusters with consistent formatting, recurring keyword structures, and predictable brand‑adjacent terminology. Clusters of domains center on a specific impersonated brand and pair that brand name with predictable thematic keywords. Financial institutions are matched with terms like login, secure, device, portal, verify, auth, or alerts. Examples include:
- rbclogin-digital[.]com
- cibcsecurity2fa[.]com
- bmosecure-webportal[.]com
- bnc-websecurity[.]com
These combinations give the domains a sense of legitimacy while also signaling the intended phishing theme (authentication, account verification, or security update).
Another domain pattern appears for brands such as Gigadat, where the naming scheme leans heavily on numerical suffixes appended to brand names; examples include gigadat-interac6302[.]com and interac-gigadat0012[.]info. The actor applies a similar pattern to logistics impersonation: DHL, FedEx, and Canada Post domains mix brand names with random numeric strings or shipment‑related vocabulary, such as mydhl725378-order442-online[.]com, parceltrackdelfedex[.]com, and canadapostshipment[.]info. Table 1 includes a few samples of domains and patterns for some of the brands the actor impersonates.
| Canadian Financial Institutions | Other high-trusted service providers |
| bmosecure-portal[.]app authentifybmo[.]com bncloginsecuriter[.]com bnc-websecurity[.]com cibc-registration-access-online[.]com cibcsecurity2fa[.]com cra-signin-partner-id[.]com etransfer-auth-cra[.]com rbcdevice-login[.]com myrbcsecureddevice[.]com tdonlineverif[.]com tdcommercial-securedlogins[.]com |
canadapostshipment[.]info adressinvalidepostescanada-enligne38846[.]info costcorebate-groceries2026[.]com mygroceries2costco[.]com dhlmanagemypack0099[.]com mydhl725378-order442-online[.]com fedexdelivery[.]ca fedexca-orderstatus[.]link gigadat-interac-0910[.]com gigadat-claiminterac[.]info |
| Table 1. Sample of lookalike domains used to impersonate legitimate financial institutions and businesses | |
Scams
Cryptocurrency Theft
A recurring theme in the threat landscape is the fake airdrop giveaway, which leads to cryptocurrency theft via a wallet drainer. Actors use Keitaro to track and filter/redirect visitors to their lure websites. Incident reporting shows millions in losses from Solana wallet drainers, with stolen assets including USDT/USDC, BONK, ZERO, and SOL.
In legitimate settings, blockchain projects run airdrops to distribute free tokens to eligible wallet addresses. These often belong to early users and are a way for the project to bootstrap communities, decentralize ownership, and market new launches. Threat actors piggyback on that pattern. They promise free tokens, then drive targets to connect their wallets and approve malicious transactions or to download wallet‑drainer kits.
In practice, unsolicited airdrop tokens are frequently illiquid, unsellable, or outright impersonations designed to trigger risky clicks. Despite this, many owners have only a surface-level understanding of tokens and overestimate their cash-out value. Cryptocurrency token giveaway scams exploit this misunderstanding and hit key psychological levers, adding artificial scarcity (“first-come, first-served”) and urgency to short‑circuit due diligence and push a wallet connection.
One common variant impersonates Phantom, which is a multichain wallet application and not a token project. Phantom has explicitly stated it has no plans to launch a token or conduct an airdrop, so any “Phantom token” pitches are almost certainly fake or impersonation tokens used as scam pretexts.
For example, during the week of December 13, 2025, a threat actor conducted a large spam campaign that sent thousands of emails from a spoofed address hello[@]phantom[.]com. The email contained an HTML body message disguised as a real Phantom promotion letter (see Figure 15).
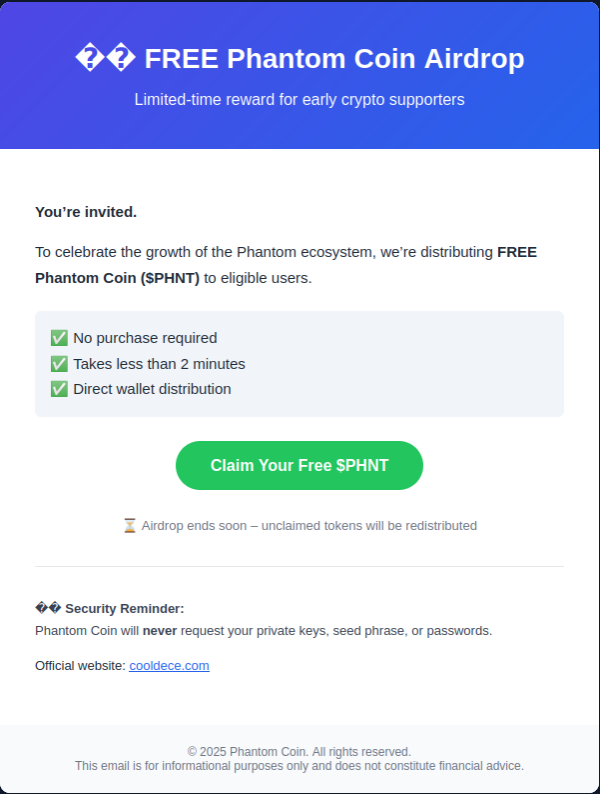
Figure 15. Spam email message with fake giveaway lure
The emails instructed victims to claim free Phantom tokens on the actor’s fraudulent website hXXps[:]cooldece[.]com, which used Keitaro to track visitors. Figure 16 shows the website impersonating the Phantom platform.
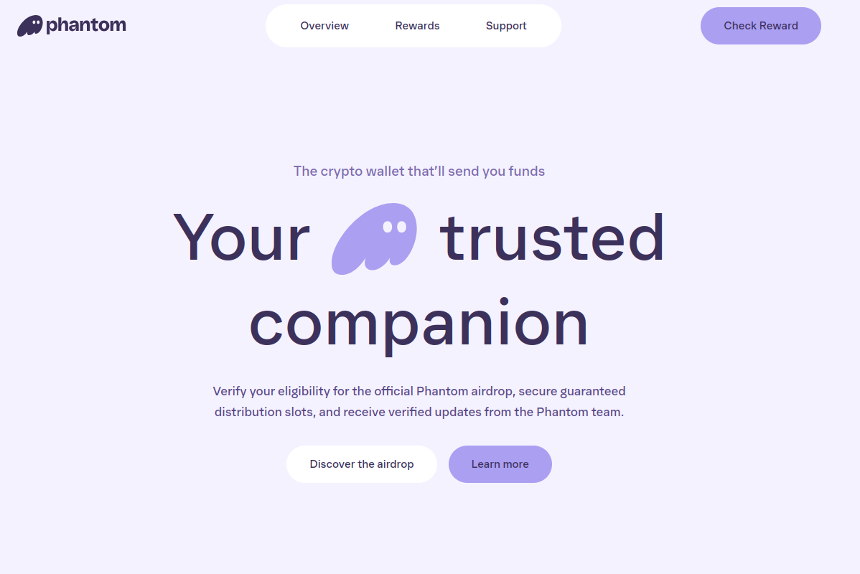
Figure 16. Scam page impersonating Phantom
When victims stepped through the reward claim process, the website redirected them to another malicious location: hXXps[:]//honknft[.]com/connect/rh7_1a7r72zi-kk4k4z?b=1. From here, the actor instructed victims to connect their Phantom wallet to receive the free tokens. In this scam, the actor simply used the free token promise to lure the victim into connecting their wallet and signing a malicious transaction. This action authorizes the actor to drain liquid assets such as USDC/USDT, popular SPL tokens, and NFTs that already exist in the victim’s wallet. There are drainer kit tools that help actors easily run these transactions.
Many of this actor’s previous campaigns involved a different giveaway scam (Figure 17). Their wallet drainer JavaScript functions were heavily obfuscated. Their lures instructed victims to “turn on Blind Signing and Debug Data.” By doing so, victims turned off ledger device safeguards and approved opaque smart contract interactions they could not verify in a human readable way.
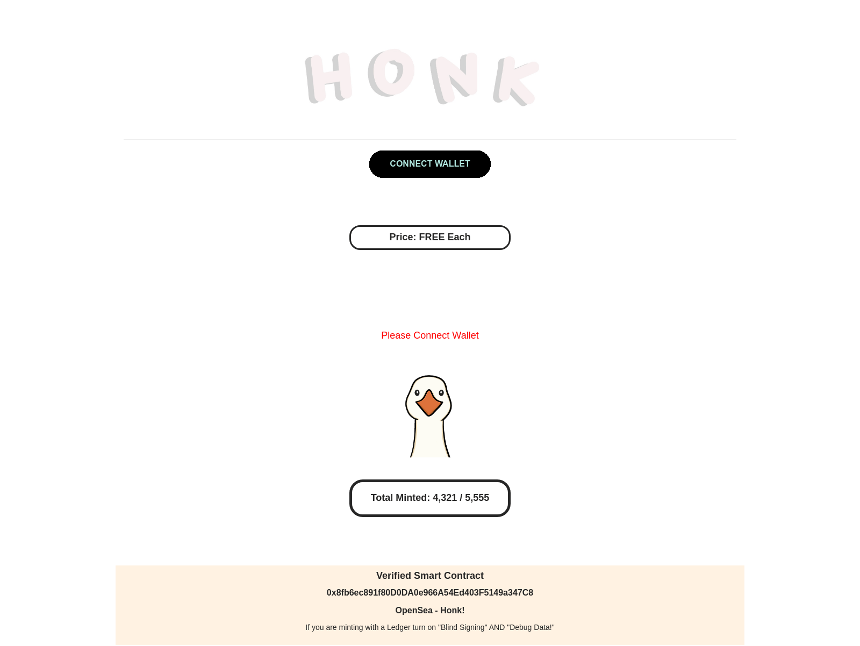
Figure 17. Token wallet drainer lure
Domain registration details and hosting history for honknft[.]com indicate the actor is likely based in Russia. The registrant location fields show Moscow, Russia, and although the site sits behind Cloudflare, passive DNS indicates the domain’s real IP address is 158[.]94[.]208[.]165. That address is managed by omegatech[.]sc (AS202412), an ASN registered only a couple of months ago as of this writing. Its upstream provider is aurologic GmbH; open‑source reporting has described aurologic as an upstream provider for networks associated with cybercrime, disinformation, and other forms of abuse, including some with links to Russia.
Additionally, we traced honknft[.]com to an Ethereum-based NFT collection called Honk! ($HONK). On Etherscan, the token page classifies it as an ERC‑721/NFT and links to honknft[.]com/mint. The token was launched in January 2023 — the same month we saw the first attack instance and campaign from this wallet drainer actor. As of this writing, the token shows a history of nearly 25,000 token transfers (see Figure 18). Based on infrastructure overlap and campaign timing, this NFT collection is likely dedicated to the actor’s wallet draining operations.
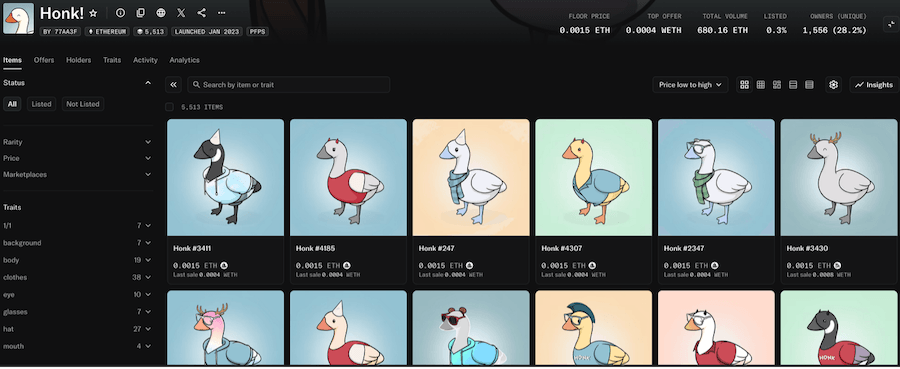 Figure 18. Honk! NFT collection page on opensea.io associated with wallet-draining campaign
Figure 18. Honk! NFT collection page on opensea.io associated with wallet-draining campaign
Spoofing Investment Companies
The actors covered in our first blog in this series (Inside Keitaro Abuse: A Persistent Stream of AI-Driven Investment Scams) create fabricated investment companies. In contrast, this actor impersonates legitimate investment and financial businesses. They use domains with no distinct pattern rather than keyword lookalike domains (Table 2), which helps them evade detectors that rely on identifying brand‑similar domains. The page content is where they spoof real companies, and in many of the examples we observed, the impersonations target multiple investment and financial businesses across different countries (Figure 19.1 and 19.2).
| Indicator | |
| azgrvfra[.]com ca24watch[.]com dailycrepoton[.]com digitalwealth-au[.]com iralfdgs[.]com |
moplih[.]com newtotalca[.]com quietfostdio[.]com someotherbox[.]com uzelart[.]com |
| Table 2. Sample domains for sites with content that impersonates legitimate businesses, but the domains are not lookalikes | |
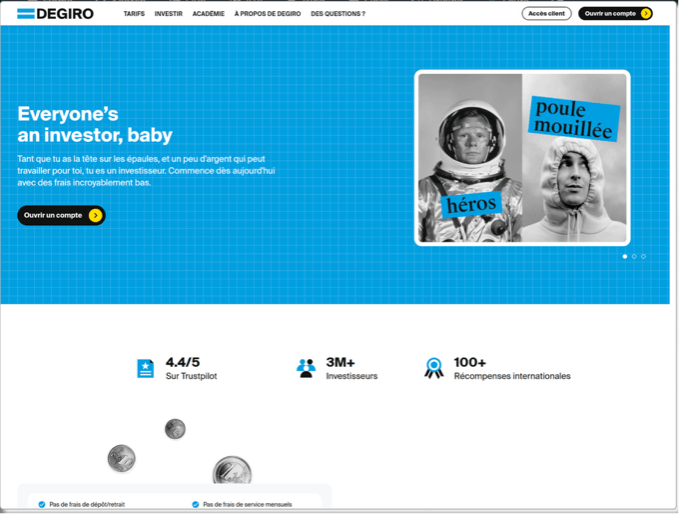
Figure 19.1. Investment scam page for burkespitbbq[.]com, which impersonates DEGIRO, a European online broker based in the Netherlands
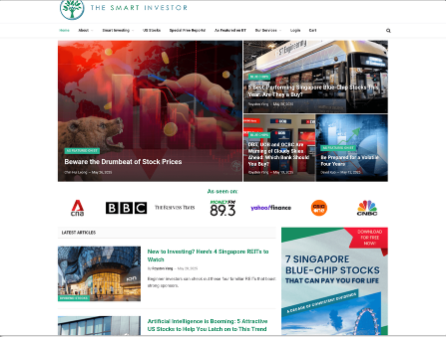
Figure 19.2. Investment scam page for linda-makeup[.]com, which impersonates a Singapore-based financial education platform
Health and Fake Shops
Dubious healthcare products are a problem that predates the digital era. Modern malvertising campaigns often digitally promote “snake oil” products which often include supplements like keto gummies promising rapid weight loss, or services that make dangerous, unsubstantiated claims about curing serious ailments. The purveyors of these goods exploit consumer anxieties and vulnerabilities to push products that are at best unproven, and at worst actively harmful.
The digital ad campaigns marketing these products and services will often try to create a false sense of urgency (“only 100 bottles left,” “claim yours now”) and are supported by numerous fake reviews and testimonials on verbose sales pages. It’s typical for prices to be inflated as well.
Ad platforms that take marketplace quality seriously will have policies in place against these types of campaigns, so the affiliates that promote these offerings will often have to rely on cloaking to circumvent any safeguards.
We have solid examples of these types of health scams with Keitaro present, from the fourth quarter of 2025. Figure 20 below shows one such example.
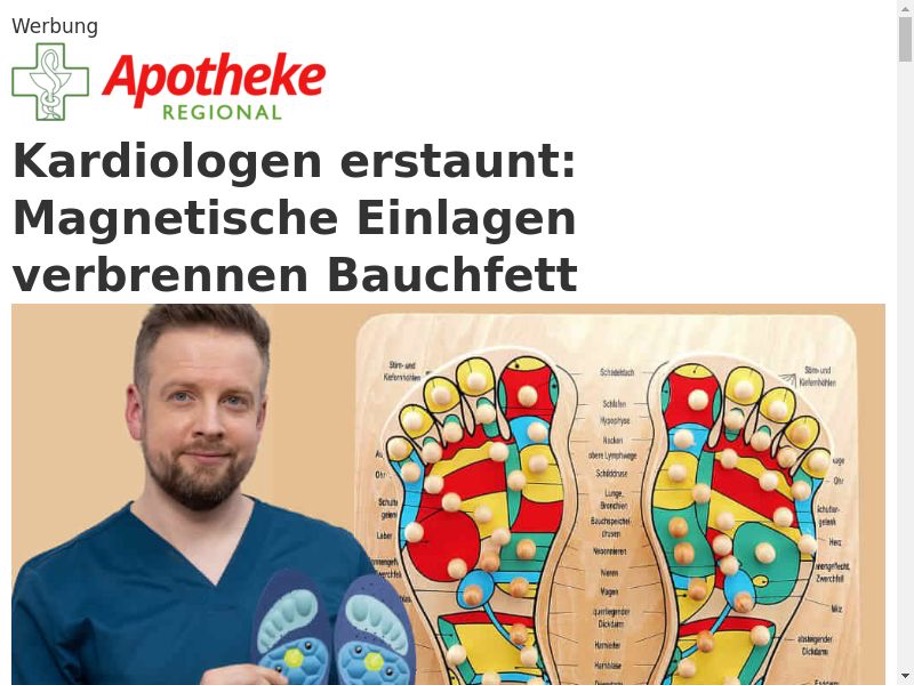
Figure 20. Health scam hosted on health[.]tenerium[.]org
TheNovosti
TheNovosti is an Eastern European-origin actor running large-scale cloaked campaigns that trick users into opting into malicious push notification subscriptions, often via fake “half-loaded” page templates. After opt-in, notifications escalate to a broad range of malvertising chains. Ad creative is typically health (Figure 21) or pension-themed clickbait targeting elderly users (e.g., garlic cures, sugar factoids). This actor is known for extremely high domain churn (~4,000 domains per week at peak) and believed to be the umbrella actor responsible for several related clusters. This actor has used Keitaro for cloaking.
Figure 21. TheNovosti clickbait ad leading victims to terrainane[.]com
Unnamed Health Scam Actor
This actor runs health product scam shops designed to promote supplements and other products, and will eventually steal the user’s financial information. The domains for these shops are primarily advertised through Facebook ads targeting multiple regions in various languages. Both the scam pages and Facebook ads rely on social engineering tactics to entice users and create urgency through misleading “miracle cure” narratives and supposedly expiring supplement deals. Users attempting to access the sites outside of the actor’s targeted locations will be redirected to legitimate pages like YouTube and Amazon; cloaking enabled via Keitaro. Examples of the Facebook ads and scam pages can be seen in Figures 22 and 23.
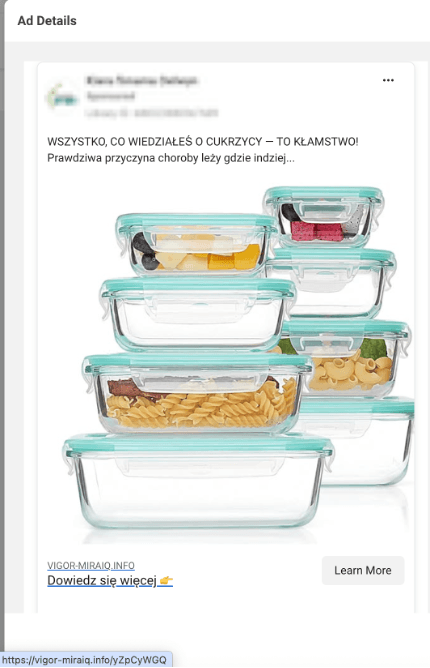
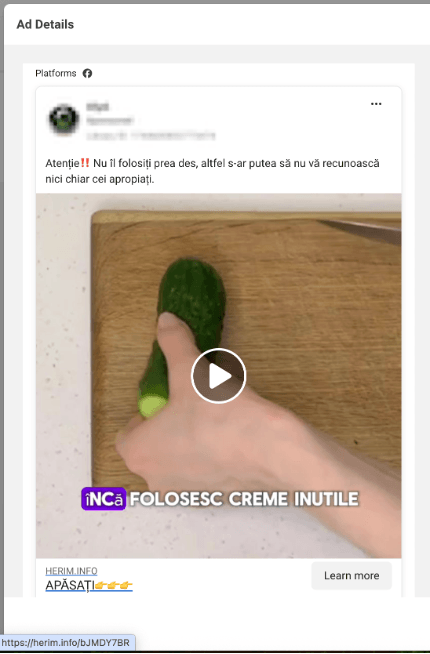
Figure 22. Facebook ads associated with health product scam shops
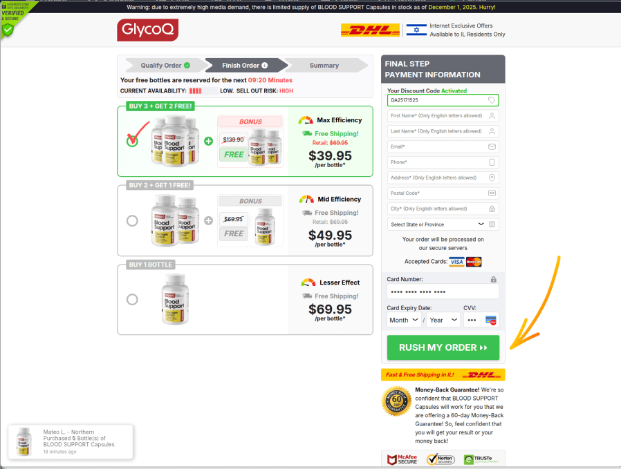
Figure 23. Screenshot of one of the fake shop pages
The domains show a clear pattern of bulk‑generated, disposable infrastructure centered on cheap, low‑reputation TLDs, most commonly .top, .click, .today, .info, .store, .shop, .life, .biz, and .pro, with the occasional generic .com. Naming conventions rely heavily on simple, hyphenated keyword pairs tied to broad themes like news, health, wellness, fitness, or lifestyle, alongside numerous short, pseudo‑random strings indicative of automated registration. Table 3 shows a sample of such patterns.
| Hyphenated Themes | Randomly Generated |
| trending-now[.]today the-social-spot[.]com fitness-zenew[.]info curated-nest[.]pro boost-core[.]today coreflow-news[.]info tipboost-info[.]com strong-tips[.]info life-booste[.]com energy-zone[.]top |
pilyf[.]life nywav[.]life rujas[.]biz qezybu[.]com gyruvi[.]top suxady[.]top jaceviu[.]shop ziqiwui[.]click jexyni[.]top qiqaly[.]top |
| Table 3. Sample domains grouped by the techniques used to generate them | |
The campaign also shows indications of using a TDS, with multiple redirect hops observed across samples. In one instance, the presence of top9mediatrk[.]com in the redirection chain suggests the likely use of TDS‑style infrastructure to route and manage traffic before ultimately leading users to the health‑product scam pages.
More Investment Scams
HircusPircus
Tracked since 2021, HircusPircus is an international scam group that advertises fraudulent investment opportunities. They typically use the tactic of abusing brands as opposed to celebrities, which is less likely to be detected by ad platform security mechanisms.
This actor has been influential enough to serve as a reference point for categorizing similar investment scam actors and sub-clusters from a detection perspective. HircusPircus differs from FaiKast (an investment scam actor that leverages AI in their investment scams and therefore was included in blog 1 of this series) in that they do not rely on deepfake personas to drive victims to their scams. Furthermore, it’s very unusual to see this actor implement cloaking in their campaigns. However, we did observe them running Keitaro with the HideClick cloaking kit enabled in a prominent, high-volume campaign (hosted on investarmco[.]com) at the end of October 2025. See Figure 24.


Figure 24. HircusPircus ad sample for an investment scam impersonating ADNOC run on investarmco[.]com
Typical HircusPircus TTPs include:
- Ads are served through programmatic advertising that anchor on investing-related copy (Figure 24 above)
- Landing pages promote fake savings products (Figure 25 below)
- Campaigns use domains with financial-sounding names and sometimes reference real companies to add credibility

Figure 25. HircusPircus landing page impersonating Aramco, hosted on investarmco[.]com
AirportArrest
AirportArrest is an actor behind cloaked investment scams that span multiple countries including Canada, Italy, Switzerland, and others. They’re an unusual player in investment scam malvertising as their clickbait of choice is fake content of people getting arrested. The white pages are highly localized and often feature real news about the targeted city, such as various infrastructure projects.
Ads and landing pages typically have some sort of scandalous law enforcement angle such as those shown in Figures 26 through 28.

Figure 26. AirportArrest clickbait ad sample on hotelbiloxi[.]com
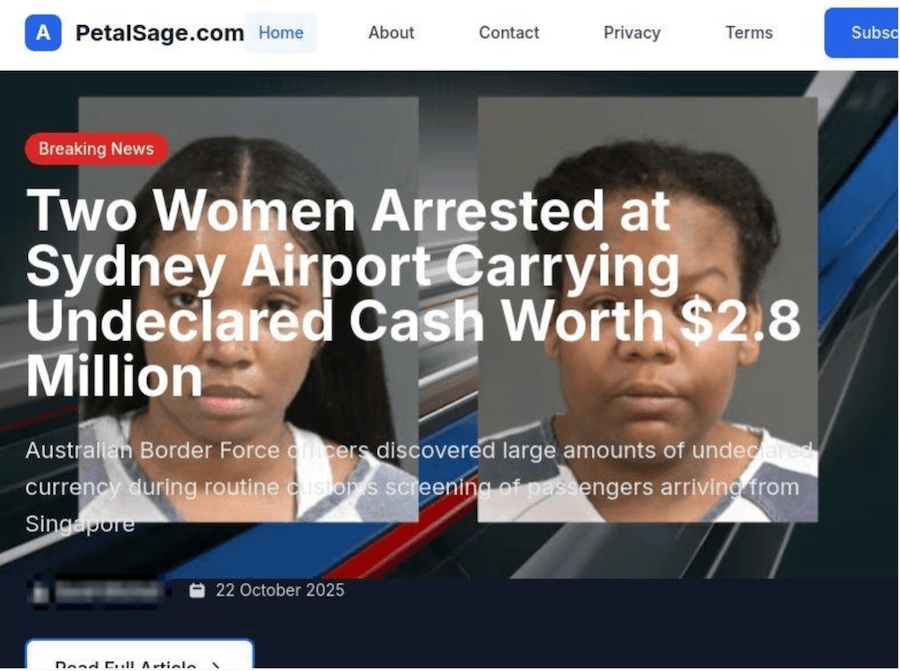
Figure 27. AirportArrest landing page with fake story on petalsage[.]com
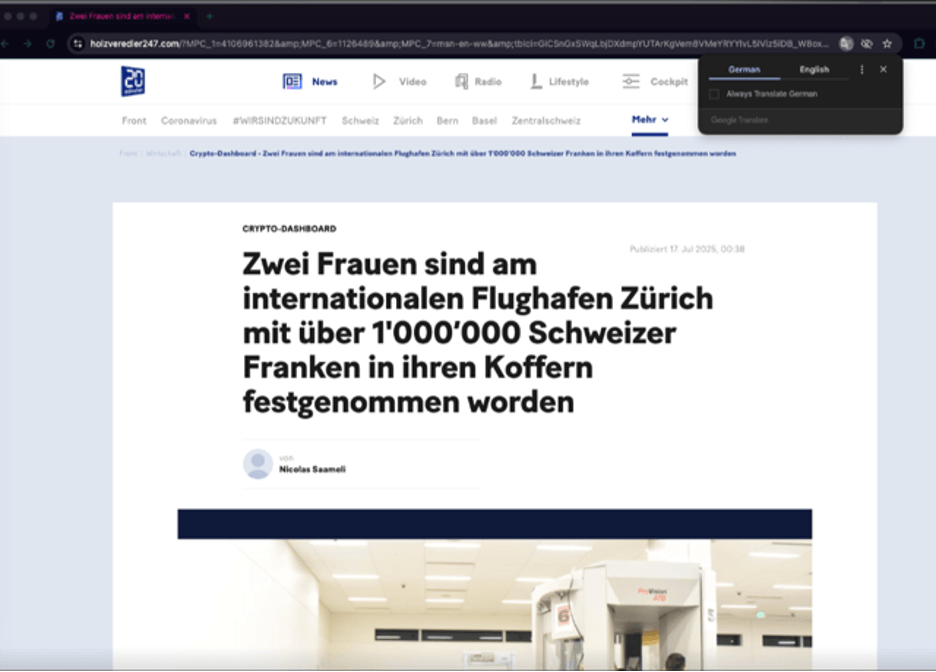
Figure 28. AirportArrest landing page impersonating a legitimate news article, on holzveredler247[.]com
Illegal Content
We’ve included a dedicated section on Illegal content, given its frequent association with Keitaro abuse. However, this activity, including online gambling, is typically not standalone and is instead part of larger, coordinated scam operations.
Online Gambling
Several actors we have observed abusing Keitaro services lead users to online gambling sites. In one notable example, the domains redirect multiple times before reaching the final landing page, strongly suggesting the use of a TDS (Figure 29). The actor uses hostnames like leadshub[.]trk-links[.]com and tds[.]favbet[.]partners in redirect chains routing to gambling pages (Figure 30). The presence of terms like “trk” and “tds” in these hostnames, along with the multiple redirections, are TTPs commonly associated with TDS infrastructure.
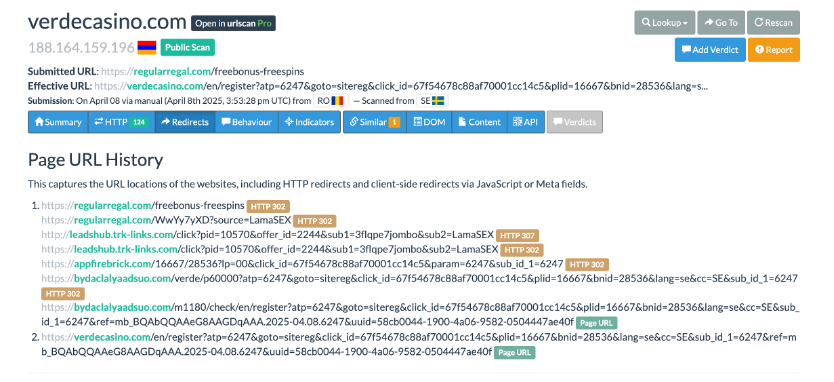
Figure 29. Multiple redirections and the presence of the domain trk-links[.]com suggest a TDS
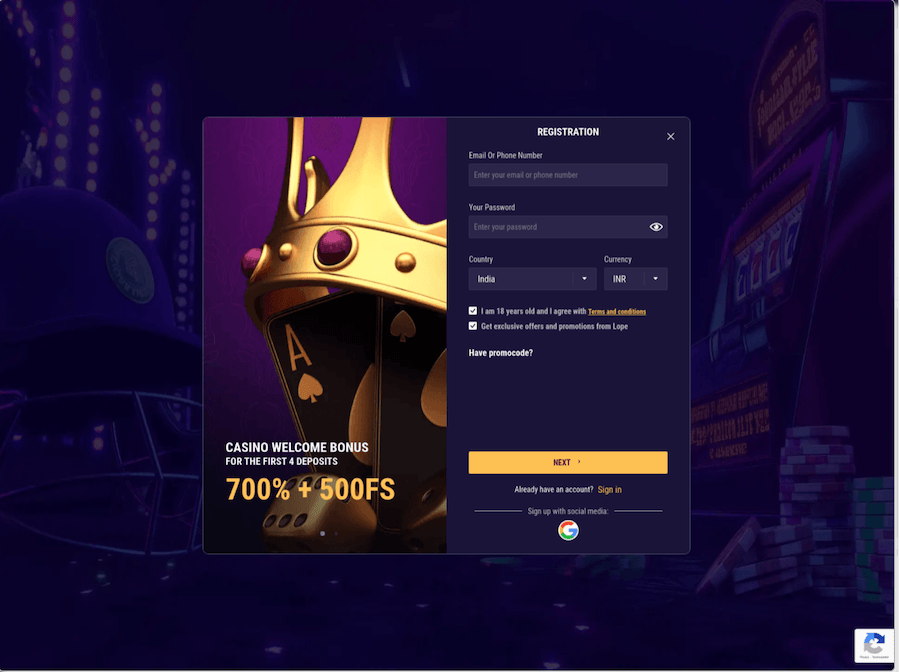
Figure 30. Example of a gambling page; there are many different templates and the content can look completely different
This actor uses a variety of patterns when creating their SLDs, likely to diversify their infrastructure and make it more difficult to detect and block the domains with a single detection rule. One common tactic this actor uses is registering the same SLD label across multiple TLDs. The examples in Table 4 illustrate three variations of this approach:
- Identical SLDs across different TLDs
- Nearly identical SLDs that differ only by incremental numbers across TLDs
- Lookalike labels (e.g., variations resembling “telegram”) registered on multiple TLDs sometimes paired with accompanying terms like “link” or “hub”
| Same or similar SLD label, different TLDs | ||
| click-link[.]online click-link[.]store click-link[.]space |
linkhub1.online linkhub2.space |
talagram[.]online talagram[.]store |
| Different variations | ||
| hublink1[.]space hublink2[.]space hublink3[.]space hublink4[.]space |
your-link[.]online your-lnk[.]online yourlnk[.]online |
invitezone[.]space invitationlink[.]space invitehub[.]site |
| Table 4. Sample domains grouped by different domain generation techniques; TLDs such as .space TLD and .online TLD have low reputations | ||
Adult Content
We uncovered an actor that appears to be hijacking domains to deliver pornography and dating-related content. At least 75% of the domains associated with this activity exhibited lame delegation at some point—meaning the authoritative name server(s) that the domain is delegated to does not have information about the domain and therefore cannot resolve queries—making it susceptible to takeover via a Sitting Ducks attack. A lame delegation creates a gap where certain exploitable DNS providers allow anyone to “claim” the vulnerable domain’s DNS configuration without having access to the legitimate registrant’s account, enabling quiet and effective hijacking. Below is a sample of titles from the pages involved in this activity:
- “Deep talk. Slow burn. Real interest.”
- “You’re not the only one tired of surface-level.”
- “A little flirt never hurt. Start with a smile.”
- “This isn’t fast food dating. It’s the good stuff.”
The domains in this actor’s cluster also show very sparse and inconsistent infrastructure patterns—different registrars, hosting providers, and DNS configurations—which is atypical for a threat actor intentionally building their own domain ecosystem, but fully consistent with opportunistic hijacking of abandoned or misconfigured properties. As illustrated in Figure 31, the registration dates span more than two decades, further supporting that these domains were not created by a single actor but repurposed after periods of neglect.
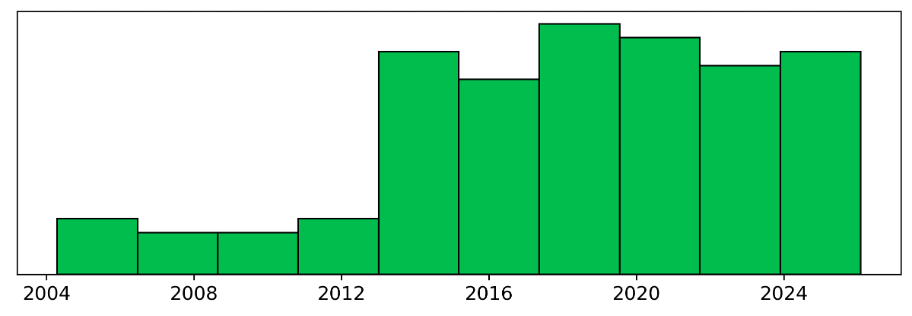
Figure 31. Distribution of creation dates for domains associated with an unnamed actor involved in domain hijacking activity
Since October 2025, every observed domain linked to this actor redirects to the adult content hosted on yellowusheart[.]net via TDS domain meetdatefind[.]com, although in some instances the redirection chains end at the TDS domain. This consistent redirection pattern—despite the starting domains’ unrelated origins and infrastructure—strongly supports the conclusion that the actor is using hijacked domains as disposable entry points. By taking control of previously legitimate or dormant domains, the actor inherits any existing reputation or residual traffic and avoids domain acquisition costs, all while making the campaign’s structure and origins difficult to trace. Figure 32 shows the redirection chain.
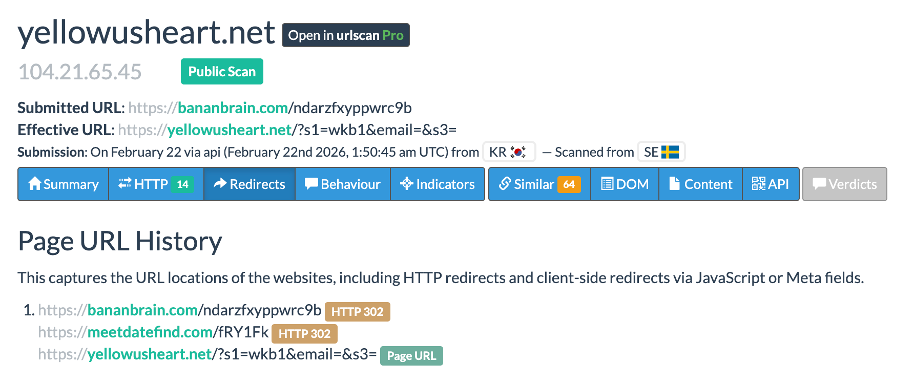
Figure 32. Redirection chain for the TDS routing users from hijacked domains to porn/adult websites
What’s Next
Part 3 closes the series by stepping back from individual clusters to map the ecosystem dynamics behind Keitaro‑enabled operations:
- Trendlines & inflection points: A high‑level overview of notable shifts and trigger events that catalyzed activity patterns across campaigns using Keitaro.
- Feature analysis: How specific Keitaro features can be or are being weaponized in practice, supported by representative case vignettes.
- Cybercrime disruption: A candid account of our work with Keitaro’s leadership to establish an abuse‑escalation channel and document success rate for fraud takedowns.
Indicators
A curated selection of indicators related to the threats discussed can be seen in the table below. A more comprehensive list of indicators can be found in our GitHub repository.
Note: These domains may be associated with inactive or stolen licenses.
| Indicators | Description |
| promoswf[.]shop promoswh[.]shop promoswn[.]shop promoswm[.]shop promoswu[.]shop |
TilapiaParabens – Rewards Scams |
| health[.]tenerium[.]org | Health Scams |
| terrainane[.]com | The Novosti |
| investarmco[.]com | HircusPircus |
| hotelbiloxi[.]com petalsage[.]com holzveredler247[.]com charityvirtue[.]com ucaboodle[.]com |
AirportArrest |
| object[.]brovanti[.]com 62[.]60[.]226[.]248 hXXp[:]//62[.]60[.]178[.]163/ce369e7324834845[.]php |
Malware download locations on Keitaro instances |
| membros[.]mtcreatingimages[.]com hXXps[:]//membros[.]mtcreatingimages[.]com/spotify |
Keitaro links used in Spotify phishing emails |
| hXXps[:]//estrategicadesenvolvimento[.]com[.]br/Webmail/web mail[.]php?email={victim@email} estrategicadesenvolvimento[.]com[.]br |
Dynamically crafted phishing links used in localized spam campaign |
| 158[.]94[.]209[.]29 | Mail server used in localized spam campaign; previously used for Remcos RAT C2 |
| adressinvalidepostescanada-enligne38846[.]info authentifybmo[.]com bmosecure-portal[.]app bmosecure-webportal[.]com bnc-websecurity[.]com bncloginsecuriter[.]com canadapostshipment[.]info cibc-registration-access-online[.]com cibcsecurity2fa[.]com costcorebate-groceries2026[.]com mygroceries2costco[.]com cra-signin-partner-id[.]com dhlmanagemypack0099[.]com etransfer-auth-cra[.]com fedexca-orderstatus[.]link fedexdelivery[.]ca gigadat-claiminterac[.]info gigadat-interac-0910[.]com gigadat-interac6302[.]com interac-gigadat0012[.]info interac-gigadat15[.]info mydhl725378-order442-online[.]com myrbcsecureddevice[.]com parceltrackdelfedex[.]com rbcdevice-login[.]com rbclogin-digital[.]com rbcsecurityservices[.]com tdcommercial-securedlogins[.]com tdonlineverif[.]com |
Domains used by an unnamed lookalike actor |
| cooldece[.]com honknft[.]com hXXps[:]//honknft[.]com/connect/rh7_1a7r72zi-kk4k4z?b=1 |
Indicators used in wallet draining scams impersonating the Phantom platform. |
| azgrvfra[.]com ca24watch[.]com dailycrepoton[.]com digitalwealth-au[.]com iralfdgs[.]com moplih[.]com newtotalca[.]com quietfostdio[.]com someotherbox[.]com uzelart[.]com burkespitbbq[.]com linda-makeup[.]com |
Domains used by an actor spoofing investment companies |
| trending-now[.]today the-social-spot[.]com fitness-zenew[.]info curated-nest[.]pro boost-core[.]today coreflow-news[.]info tipboost-info[.]com strong-tips[.]info life-booste[.]com energy-zone[.]top pilyf[.]life nywav[.]life rujas[.]biz qezybu[.]com gyruvi[.]top suxady[.]top jaceviu[.]shop ziqiwui[.]click jexyni[.]top qiqaly[.]top |
Domains used by an unnamed actor running heatlhcare product scams |
| top9mediatrk[.]com | TDS domain seen in association with the same actor in the row above. |
| click-link[.]online click-link[.]store click-link[.]space hublink1[.]space hublink2[.]space hublink3[.]space hublink4[.]space invitezone[.]space invitationlink[.]space invitehub[.]site linkhub1.online linkhub2.space talagram[.]online talagram[.]store your-link[.]online your-lnk[.]online yourlnk[.]online |
Domains used by an unnamed actor associated with online gambling |
| leadshub[.]trk-links[.]com tds[.]favbet[.]partners |
TDS domains seen in association with the same online gambling actor in the row above |
| yellowusheart[.]net meetdatefind[.]com |
Domain and TDS domain seen in association with an unnamed actor hijacking domains to deliver pornography. |








