Authors: Zafir Ansari and Darin Johnson
Researchers at Infoblox use many advanced techniques to hunt threat actors and block threats early in their lifecycle. One particularly powerful approach leverages graph theory and SSL certificates to uncover threat actor operational relationships. In this blog, we describe how our certificate-driven threat intelligence system uncovers malicious domains, reveals previously unknown threat actors and consolidates existing ones by merging identities that were once thought to be separate. Without this certificate analysis approach, we would miss approximately 57 percent of these certificate-related malicious domains.
The Evolution of Cyberthreat Landscapes
Identifying threat actors has become increasingly challenging as they’ve evolved beyond simple, centralized operations to sophisticated, distributed infrastructures spanning multiple domains and services. This distributed approach helps adversaries evade detection and maintain operational resilience.
While traditional security tools excel at identifying individual malicious domains through reputation feeds and blocklists, they often analyze indicators without connecting them to reveal the broader threat actor infrastructure. Understanding the complete operational footprint of threat actors is crucial—it enables security teams to anticipate future attacks, block entire campaigns rather than individual domains and gain strategic intelligence about adversary capabilities and intentions. Certificate Transparency (CT) logs offer one promising approach to bridge this gap.
Certificate Transparency Logs: An Untapped Intelligence Source
CT logs provide a comprehensive, publicly auditable record of every SSL/TLS certificate issued by a Certificate Authority (CA). While primarily designed as a transparency mechanism for web security, CT logs contain a wealth of operational intelligence.
The key insight lies in how SSL certificates handle multiple domains. When securing multiple related domains with a single certificate, operators list all domains in the certificate’s Subject Alternative Name (SAN) field, as seen in the figure below. This seemingly technical detail creates a valuable intelligence opportunity: domains appearing together in SAN fields often indicate shared operational control.
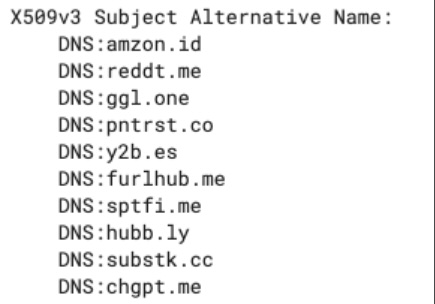
Figure 1: X509 Subject Alternative Name Domain List
The Trust Foundation of Domain Validation
The intelligence value stems from CA validation requirements. Before issuing any certificate, CAs must verify ownership of every domain listed in the SAN field through rigorous processes: DNS record modifications, email verification to administrative contacts or HTTP-based challenges. No certificate can be issued without demonstrable control over each listed domain.
This validation requirement creates a high-confidence indicator of operational relationships. When domains appear together in certificate SAN fields, they often represent shared control.
Not all certificate relationships indicate shared operational control, however. Content delivery networks (CDNs) and domain resellers often issue certificates that include customer domains alongside their infrastructure domains, creating apparent relationships between unrelated entities. Understanding and filtering these commercial relationships is crucial for accurate analysis.
The Power of Graph Theory
Individual certificates provide valuable operational intelligence, and this intelligence becomes even more powerful through transitive analysis across multiple certificates. Consider this scenario:
Certificate 1 covers domains {d1.com, d2.com, d3.com}. Certificate 2 covers domains {d3.com, d4.com, d5.com}. Certificate 3 covers domains {d5.com, d6.com, d7.com}
While domains d1.com and d6.com never appear in the same certificate, they’re transitively connected through d3.com and d5.com. This suggests potential common operational control across all seven domains, revealing infrastructure relationships invisible to individual certificate analysis.
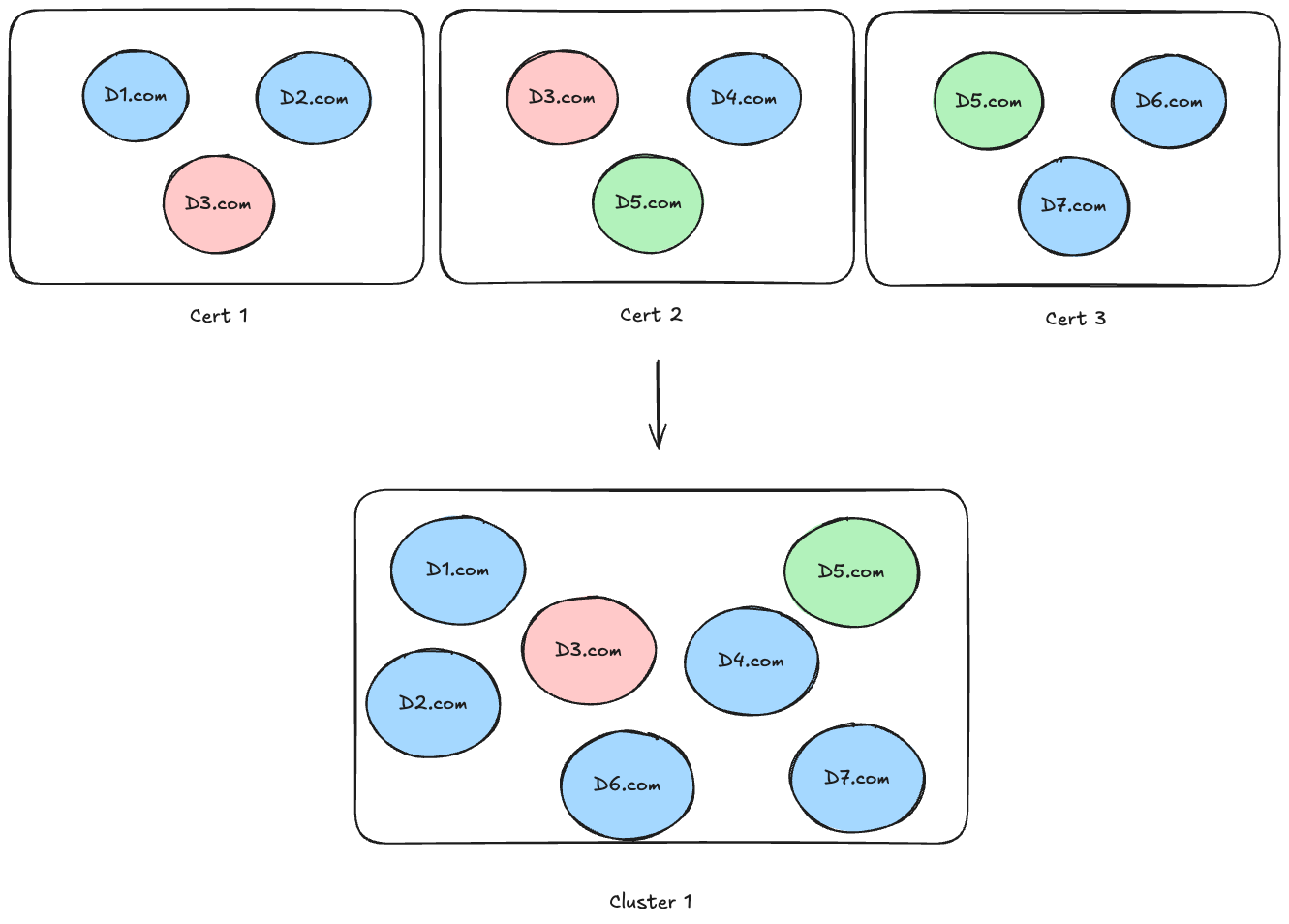
Figure 2: Cert relationships via domains
From Certificates to Operational Intelligence
Understanding these relationships at scale requires systematic analysis. Graph theory provides an elegant solution: model domains as nodes and certificate relationships as edges, then apply connected component algorithms to identify all transitively related domain groups.
The process begins with individual certificate graphs that appear separate and unconnected. However, when domains appear across multiple certificates, they create bridges that merge these separate components into unified graph components. The accompanying visualizations demonstrate this transformation: initially separate certificate graphs merge through shared domains (d3.com and d5.com in this example), revealing the complete operational component spanning all seven domains.
We process these certificate relationships daily in our production systems, analyzing millions of new certificates and maintaining real-time visibility into emerging domain components as they form and evolve across the internet infrastructure.
This mathematical approach ensures comprehensive coverage—every possible relationship within the certificate data gets captured and analyzed. Each connected component represents a potential operational entity, ranging from simple single-certificate groups to complex multi-certificate infrastructures spanning hundreds of domains.
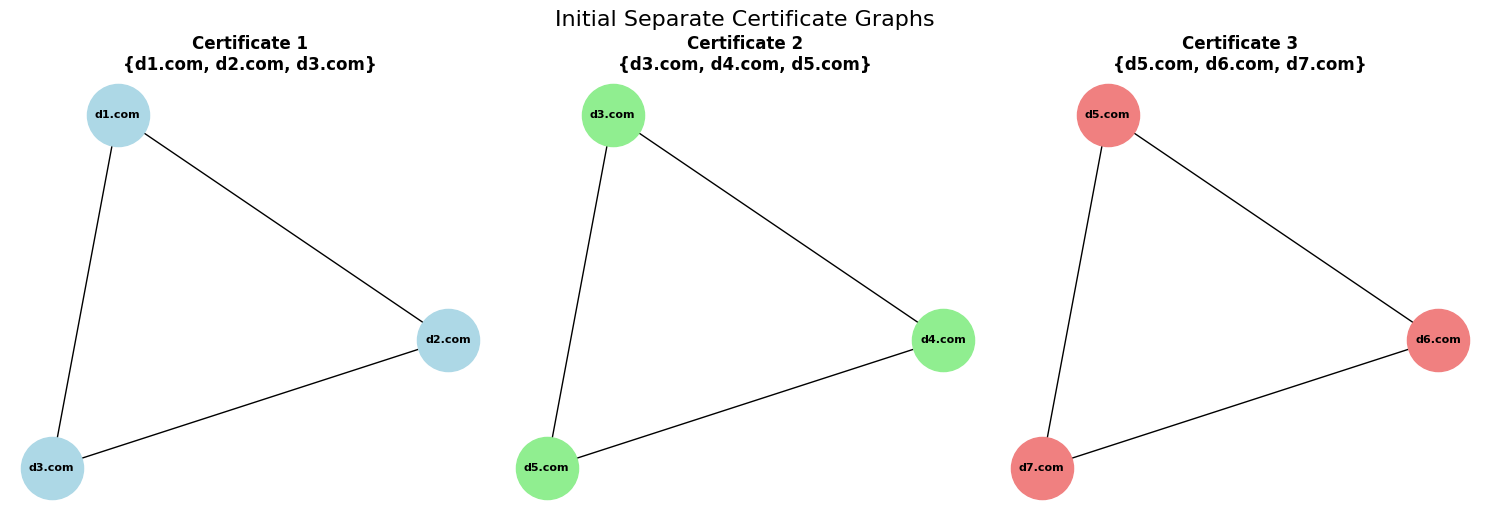
Figure 3: Initial Separate Certificate Graphs
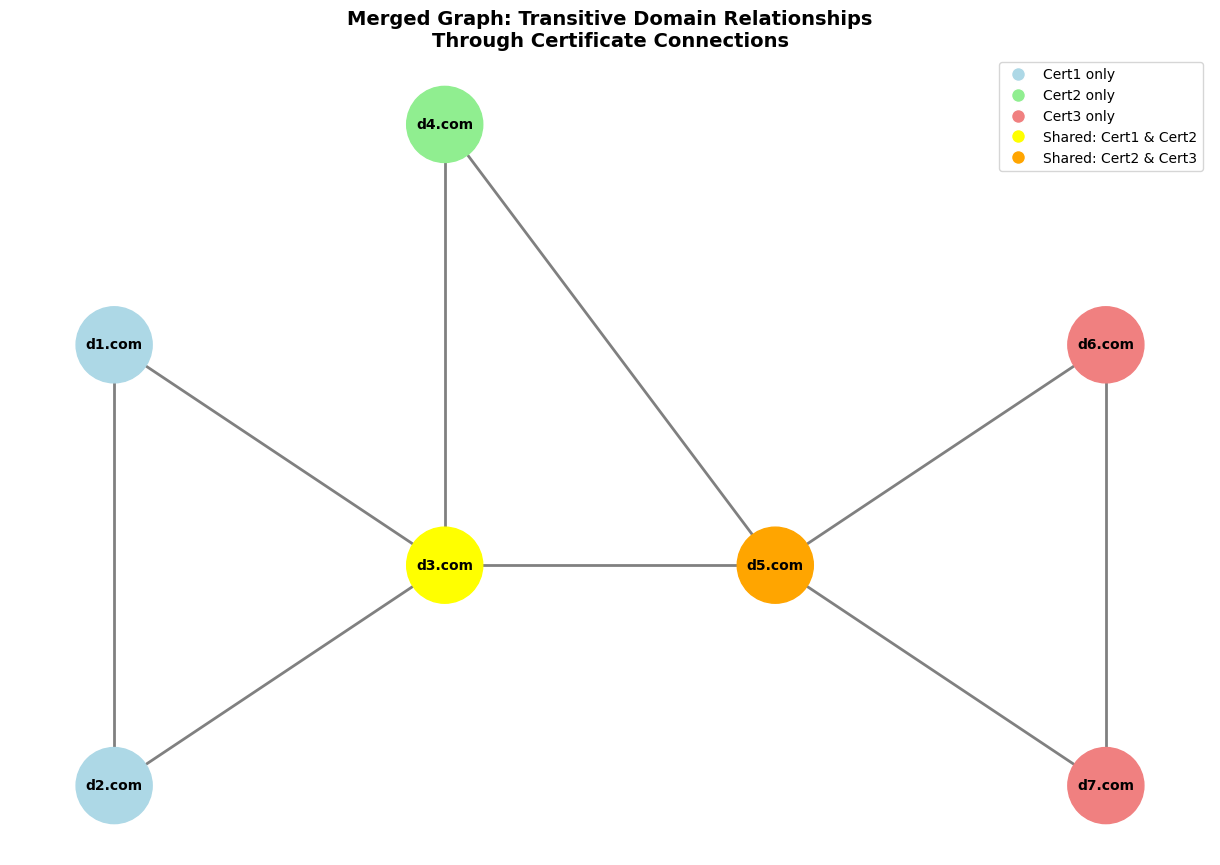
Figure 4: Merged Graph: Transitive Domain Relationships Through Certificate Connections
Temporal Complexity and Evolution
Domain components aren’t static structures. They evolve continuously as new certificates create connections between previously separate infrastructures. This evolution presents both opportunities and challenges:
Opportunities: Track infrastructure development over time (such as component mergers), identify expansion patterns and observe operational changes
Challenges: Maintain consistent component identity despite structural changes, handle complex merger scenarios and preserve historical context
We track the temporal and structural evolution of these components over time, maintaining historical continuity while adapting to the dynamic nature of certificate-based relationships. Addressing these challenges requires sophisticated tracking mechanisms that preserve component continuity while adapting to structural evolution—capabilities that become increasingly valuable as threat actors expand and modify their operational footprints.
Enriching Structural Data with Threat Context
Raw domain clusters provide structural insights, but they become actionable intelligence when enriched with threat data. This enrichment process involves querying threat intelligence feeds to categorize domains within each cluster as either known malicious/suspicious entities or unclassified domains.
This binary classification has the inherent limitation of threat intelligence coverage while enabling quantitative cluster analysis. Rather than assuming unknown domains are benign, the approach explicitly recognizes intelligence gaps and incorporates this uncertainty into risk calculations.
Attribution and Actor Mapping
Beyond individual domain classification, attribution data reveals which established threat actors operate domains within each component. This attribution information enables several analytical approaches:
- Single-Actor Clusters: Validate clustering methodology by confirming coherent threat operations
- Multi-Actor Clusters: Identify potential collaboration, shared services or operational personas
- Unattributed Clusters: Discover emerging threats and previously unknown operations
Risk Assessment and Prioritization
Converting structural relationships into actionable priorities requires quantitative risk assessment. Statistical approaches provide objective, repeatable methods for evaluating component threat levels.
Using the proportion of malicious domains within each cluster as a foundation, odds ratios and log transformations create risk scores that discriminate effectively between high- and low-risk clusters. These scores map to interpretable risk tiers that guide resource allocation and investigation priorities.
We categorize clusters into different risk tiers for prioritization of higher risk clusters and research the development of threats in low-risk clusters, enabling both immediate threat response and proactive threat hunting across the risk spectrum.
The figure 5 below shows examples of such risk clusters.
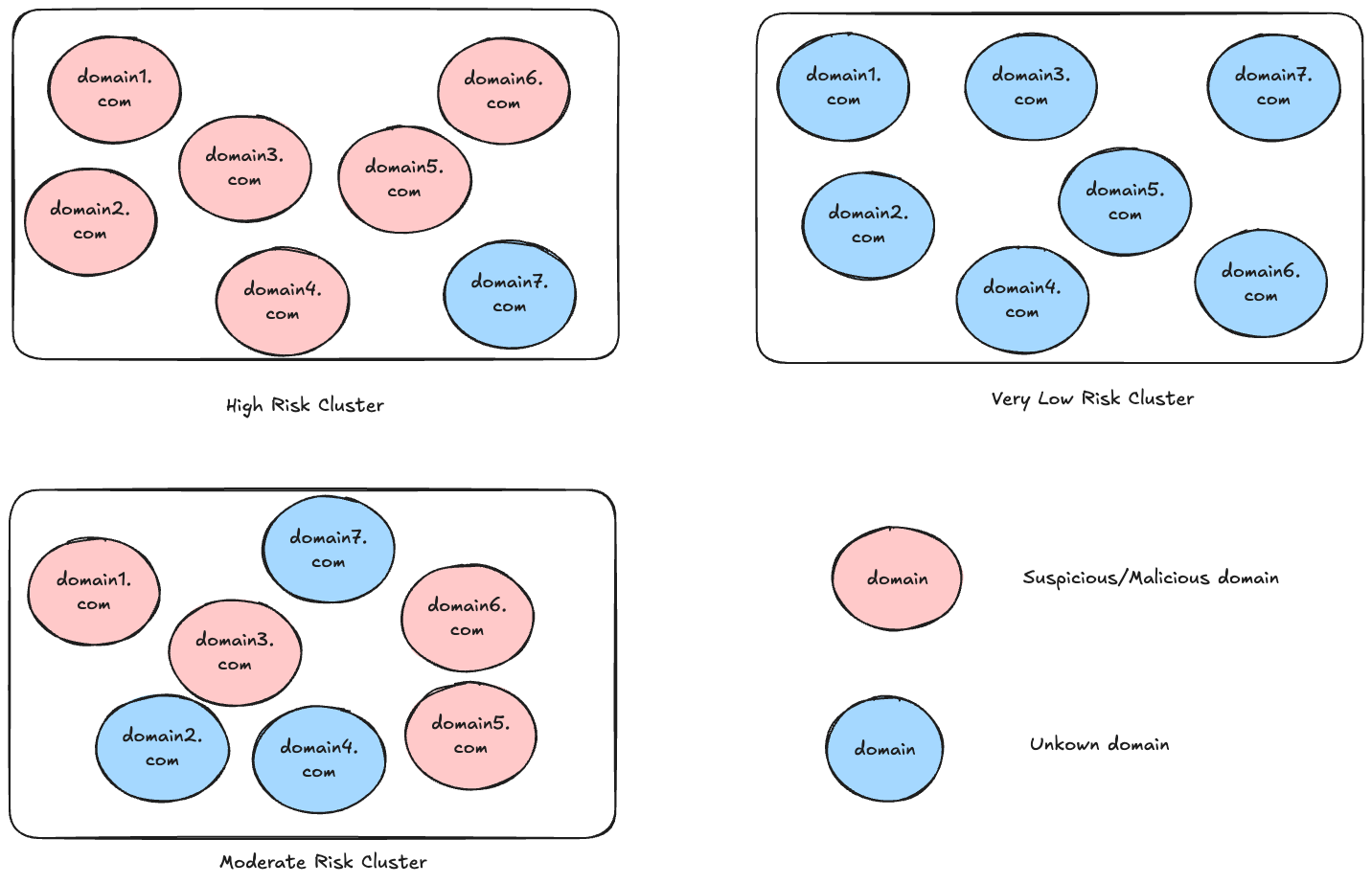
Figure 5: Sample cluster risk tiers
Expanding Intelligence through Association
One of the most powerful applications of our approach is expanding threat coverage through association analysis. When some domains in a connected component are confirmed malicious, certificate-based relationships indicate that other domains in the same cluster warrant investigation.
This “guilt by association” method leverages the core insight that domains sharing certificate infrastructure are likely under common control. If confirmed threat actors control a subset of domains in a cluster, other unflagged domains in the same cluster become high-priority investigation targets. Analysis of moderate-risk clusters alone uncovered 135 percent more malicious or suspicious domains that had previously gone undetected. The figure below illustrates this.
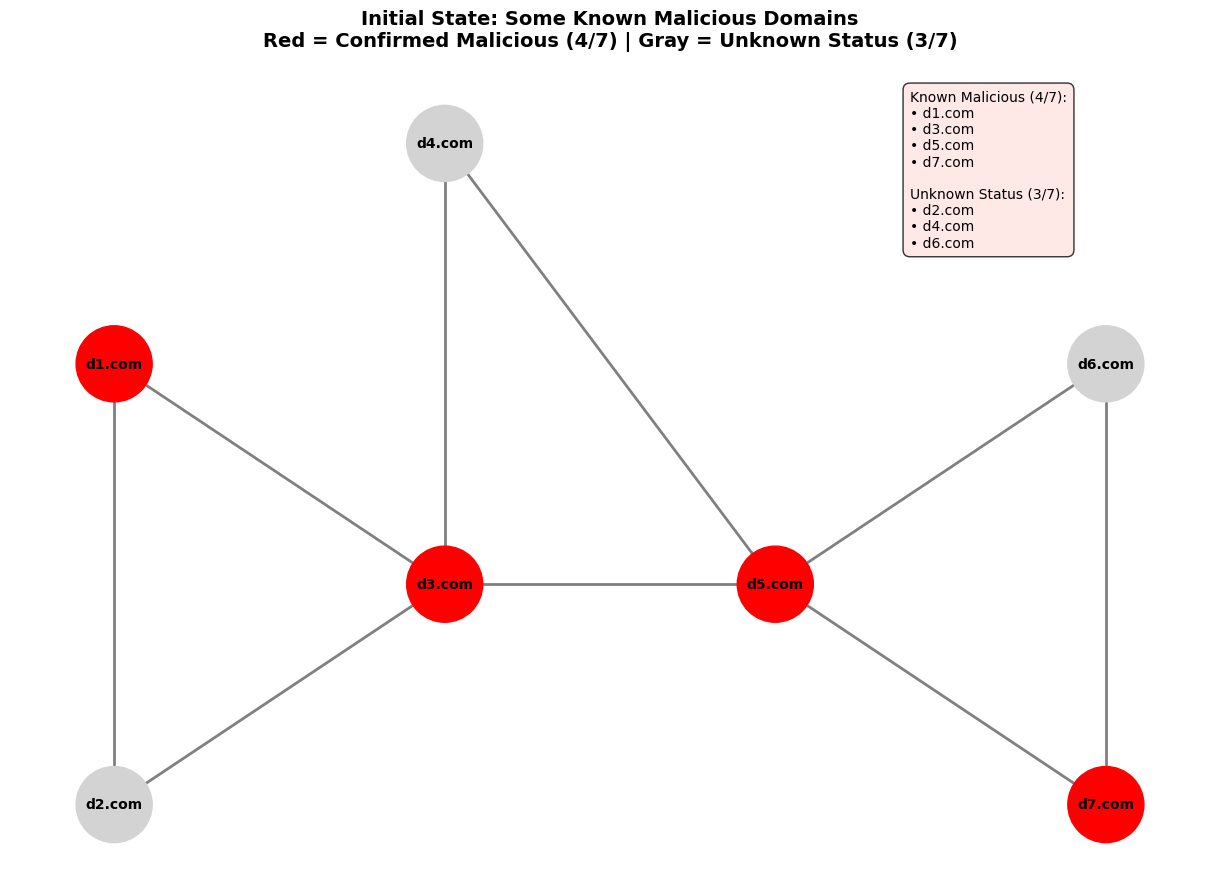
Figure 6: Domain association graph
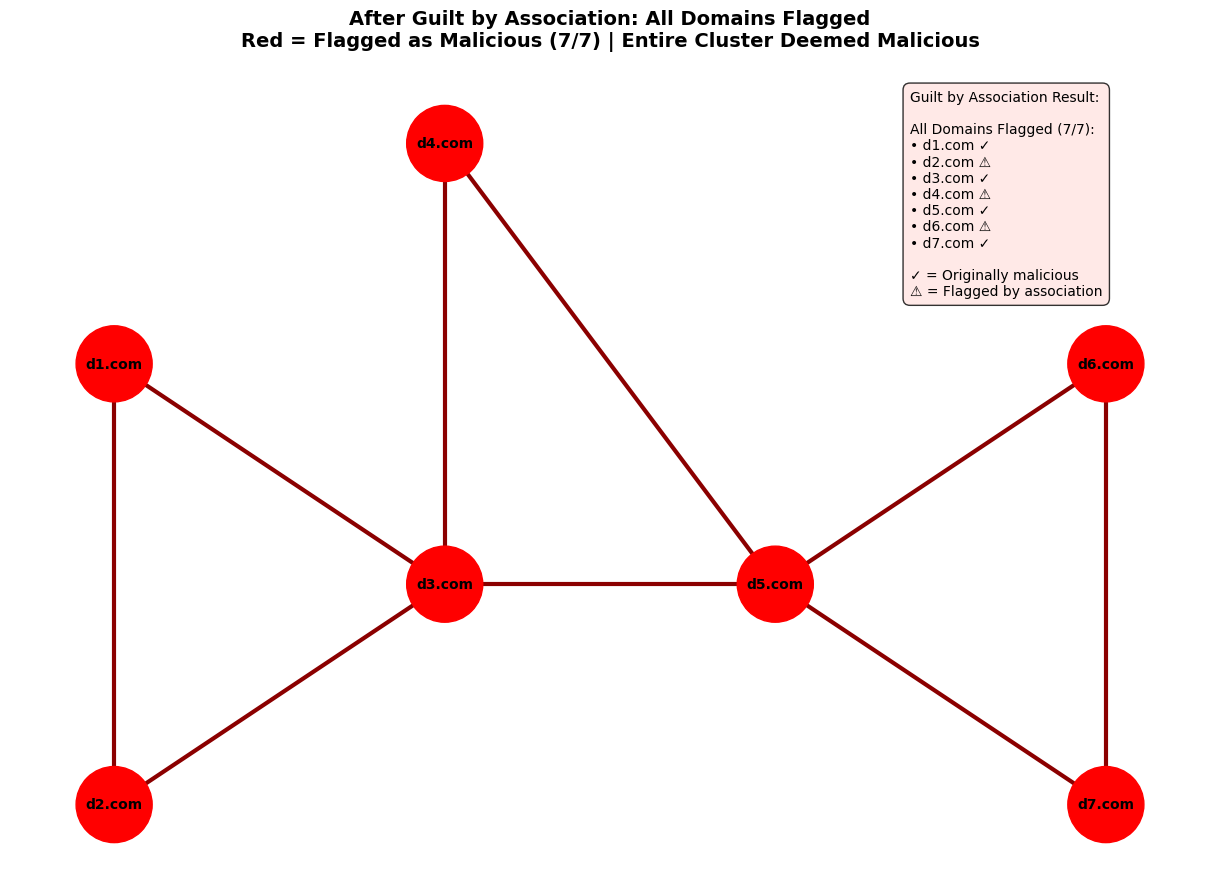
Figure 7: Guilt by association graph
Threat Actor Mapping: From Discovery to Consolidation
When we analyze domain clusters, we often find patterns in how threat actors operate. Some clusters contain domains with no existing threat intelligence. For these malicious clusters, we create new provisional threat actor identities to track their evolution over time. This capability to discover previously unknown threat actors is invaluable for early threat detection. Additionally, clusters containing multiple different threat actors provide another rich source of intelligence.
This is where things get technically interesting. For components with multiple threat actors, we use a hierarchical graph (“graph of graphs”) approach—constructing threat actor networks where actors become nodes and shared domain components (themselves graphs) create the connecting edges. Think of it like discovering that several apparently independent criminal organizations are actually using the same safe houses and supply chains.
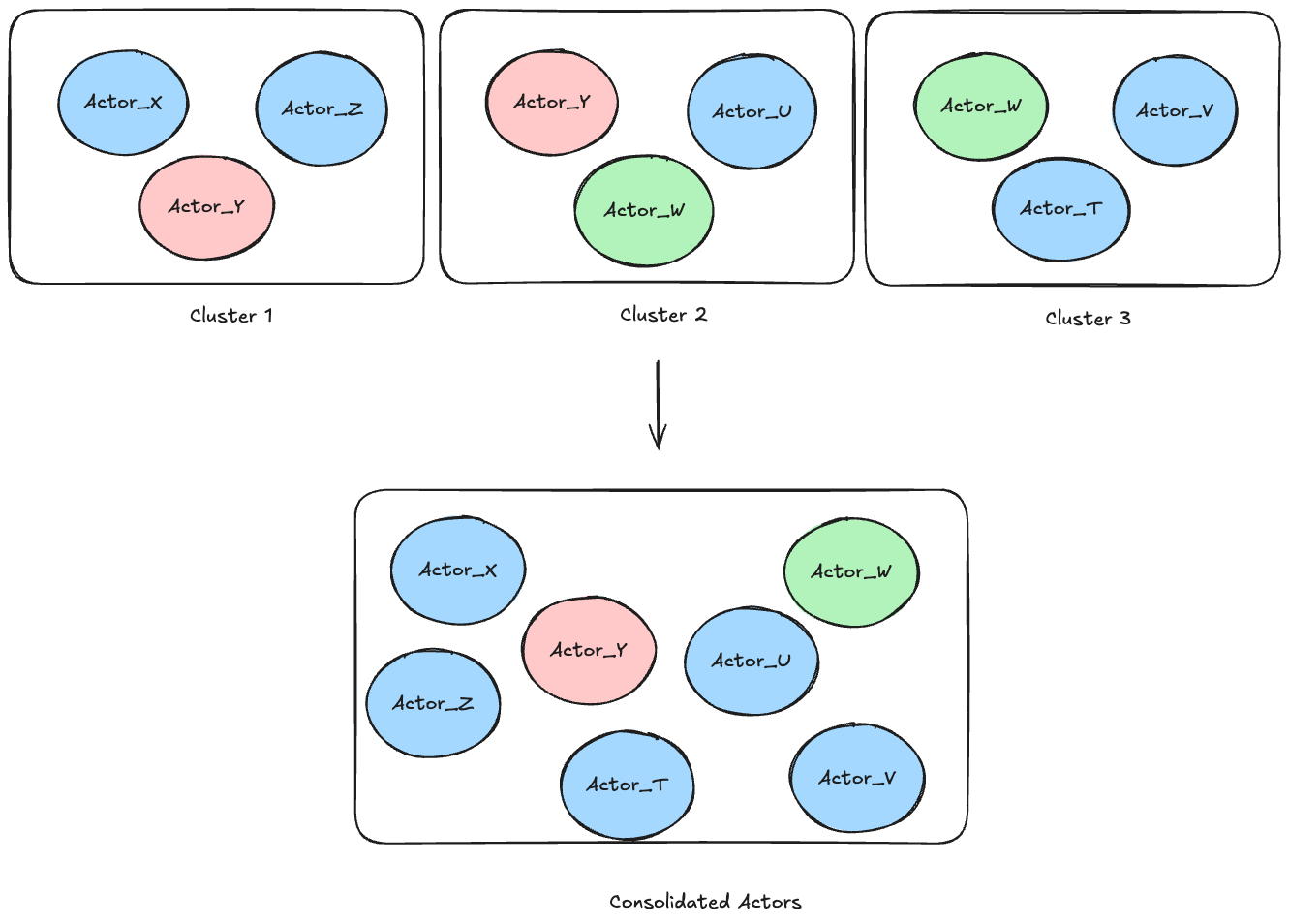
Figure 8. Actor network visualization showing how separate clusters merge into consolidated threat ecosystems
These actor networks reveal relationships that may be missed using other methods of analysis. We see actors sharing certificate infrastructure across multiple clusters, creating transitive connections between previously unrelated threat groups and forming complex ecosystems that suggest either coordination, shared services or different operational faces of the same underlying organization.
Using this hierarchical graph methodology, our production systems process millions of certificate relationships daily to identify these connections. When we apply connected component analysis to threat actor networks, we discover consolidated threat ecosystems where multiple actors collaborate, share resources or represent different operational personas of sophisticated adversarial operations.
The visualization above demonstrates this process: three separate clusters containing different combinations of threat actors ultimately merge into a single connected component, revealing a seven-actor threat ecosystem that would be invisible without this systematic graph analysis.
Practical Applications and Impact
This certificate-based approach provides several operational capabilities:
Infrastructure Discovery: Reveal comprehensive domain portfolios operated by single entities, providing visibility into organizational structures that span multiple certificates and operational domains.
Early Warning: Identify emerging threats through lower risk clusters where only a small subset of domains are flagged in traditional intelligence feeds, enabling discovery of domains as suspicious or malicious that were previously not flagged as such while simultaneously identifying the threat actors operating them, often representing the earliest indicators of new campaigns before they appear in traditional intelligence feeds. High-risk clusters, while containing predominantly malicious domains, are also valuable for discovering new threat actor identities and operational connections that may not be present in existing intelligence feeds.
Actor Relationship Mapping and Consolidation: Discover connections between established threat actors through shared infrastructure usage, revealing collaboration patterns or operational relationships. When certificate analysis reveals that apparently different threat actors are actually operational personas of the same underlying entity, we merge these identities to provide clearer intelligence pictures and reduce analytical fragmentation. Finding and accurately attributing threat actors is extremely important for understanding campaign scope and operational context.
Systematic Prioritization: Enable data-driven resource allocation through quantitative risk scores rather than arbitrary threat categorizations or analyst intuition.
Conclusion
The volume of certificates issued daily across the internet creates an opportunity to enhance threat intelligence through systematic analysis at scale. Millions of certificate relationships emerge every day, containing valuable operational connections that can strengthen security coverage when properly analyzed.
We harness this potential through our certificate transparency approach, which adds a valuable dimension to threat actor analysis and enables preemptive security measures. Our systems process millions of certificates daily, systematically discovering new threat actors operating previously unknown infrastructure, consolidating threat actor identities when analysis reveals operational connections and identifying domains that warrant further investigation. This automated intelligence pipeline transforms the rich data available in internet certificate records into actionable threat intelligence that enhances security teams’ ability to proactively identify and counter sophisticated adversaries before they can fully establish their operations. Infoblox customers using our default threat intelligence feeds automatically benefit from this pipeline.
Sample Discoveries
The following examples demonstrate the operational power of our certificate intelligence system in action. Threat actor clusters represent real threat operations, only a small fraction of which had been flagged as suspicious in open-source threat feeds like VirusTotal. Using certificate analysis, we uncovered many domains related to malicious infrastructure. What makes these discoveries particularly significant is their diversity. Our system doesn’t just catch one type of campaign, including financial fraud, credential harvesting and complex traffic distribution system (TDS) operations. The certificate-based approach reveals threat actor infrastructure across the entire spectrum of cybercriminal activities, regardless of the criminal enterprise’s ultimate purpose.
| Indicator | Note |
|---|---|
| apple-find[.]xyz, apple-findmys[.]com, com-sms[.]us, find-my-sopport-phone[.]us, find-my-supportd[.]com, icloudservi[.]me, id-my-us[.]com, iflnd-phone-us[.]com, maps-iphone[.]cloud, myphone-lost[.]com, soporte-apple[.]com, soported-appleid[.]com, support-imaps[.]com, alerta-soporte[.]us, apple-mi[.]support, apple-us-lost[.]com, find-87653[.]com[.]tr, findid-clouds[.]com, findmy-dtp[.]sa[.]com, findmyld[.]com, flnd-phone-us[.]com, icloud-id-lost[.]com, icloudsolution[.]us, soportt-apple-lost[.]com, support-lost-phone[.]com, support-lost-us[.]com, apple-lcloud[.]com[.]tr, apple-lost-lnfo[.]com, apple-supportid[.]com, apple-verifid[.]com, applefind[.]net, com-locate[.]space, icioud-aw[.]xyz, icioud-rt[.]xyz, icloud-isuport[.]com, lcloud-find-my[.]org, lost-iphone[.]us, maps-iphone[.]online, supporte-mylost[.]com, applecare-find[.]xyz, findmy-lsupported[.]com, findmyiapple[.]com, icioud-ds[.]com[.]tr, icloudfix[.]me, lcloud-mi[.]online, phone-located[.]support, soport-apple[.]com, sopport-phone-mx[.]org, support-myid[.]com, account-apple-login[.]com, com-login[.]my, find-my-phone-support[.]com, find-my-phone-usa[.]com, find-myclouds[.]com, findmy-getmaps[.]com, findmyy-apple[.]com, icioud-aw[.]com[.]tr, icloudfind[.]my, icloudkey[.]us, icloudservice[.]me, id-findmy-apple[.]com, isuporte-cloud[.]com, ldsupports[.]com, myid-maps[.]com, suport-apple-store[.]com, support-maps-id[.]com, apple-findmiy[.]com, appleld-find[.]com, device-find-apple[.]com, findmy-support-id[.]com, findmyu-supports[.]com, findsmy-id[.]com, findsmy-mapss[.]com, icioud-rt[.]com[.]tr, icloudservi[.]us, idevice-supportd[.]com, ipw[.]sa[.]com, lcloud-soporte[.]online, lostlcloud[.]com, phone-lost[.]support, apple-lnfo-lost-us[.]com, applesupportesen[.]org, find-appleld[.]my, findmyiappie[.]com, flndmy-l[.]com, lcloud-lost[.]com, lcloud-lost[.]online, located-find[.]xyz, lphoneflnd[.]com, apple-ubicado[.]com[.]tr, applemy-locate[.]com, flndcloud[.]com, icioud-ae[.]com[.]tr, icioud-he[.]site, icioud-lh[.]com[.]tr, icioud-ut[.]us, icloud-lost-mode[.]org, icloudfind[.]org, icloudgenerarsoporte[.]com, icloudservice[.]tr, icloudsolutions[.]us, id-lcloud[.]online, lcloud-fmi[.]com, ldfindmy[.]com, maps-support-findmy[.]com, apple-lost-lphone[.]com, apple-lsupports-us[.]com, find-my-icloud[.]org, supportid-findmy[.]com | Cluster of 109 Apple lookalikes |
| 618731[.]xyz, 618738[.]xyz, 618715[.]xyz, 618727[.]xyz, 618743[.]xyz, 618749[.]xyz, 618721[.]xyz, 618736[.]xyz, 618740[.]xyz, 618742[.]xyz, 618712[.]xyz, 618713[.]xyz, 618739[.]xyz, 618741[.]xyz, 618751[.]xyz, 618714[.]xyz, 618722[.]xyz, 618723[.]xyz, 618726[.]xyz, 618748[.]xyz, 618735[.]xyz, 618747[.]xyz, 618750[.]xyz, 618744[.]xyz, 618753[.]xyz, 618724[.]xyz, 618733[.]xyz, 618734[.]xyz, 618745[.]xyz, 618737[.]xyz |
Cluster of 30 registered domain generation algorithm (RDGA) domains hosting adult content |
| ethereum-gpt[.]com, coinbase-invoice[.]com, dappradar[.]biz, remix-ethereum-ide-bot[.]com | Crypto scam domains |
| qougle[.]com, goøglé[.]com, gg0[.]io, goóglé[.]com | Google lookalikes |
| telegramflp[.]cc, telegaenzm[.]top, telegrxcnm[.]cc, tlegraincm[.]cc, telegramoimn[.]cc, telegraxcim[.]top, telegracvm[.]cc, telegrasnm[.]cc |
Telegram lookalikes |
| bigsale-hu[.]com, bigsale-pl[.]com, buyadp[.]com, buykjm[.]com, evnrsn[.]com, fanskw[.]com, fwerwe[.]com, fwerwetp[.]com, jpdomall-jp[.]com, kr-discountline[.]com, kr-vipdiscount[.]com, kr-vipkrmall[.]com, kr-vipmallmall[.]com, kr-vipsaletop[.]com, linebuy-jp[.]com, mall-hu[.]com, mall-pl[.]com, mallknc[.]com, vip-hotmall-kr[.]com, vip-sale-kr[.]com, vipngf-tw[.]com, ahwae2[.]com, buyjdn[.]com, gr-hotsale[.]com, hotmall-ro[.]com, hotsale-hu[.]com, jponline-jp[.]com, kr-linebuy[.]com, kr-vipluckybuy[.]com, kr-vipsalesale[.]com, kr-vipshopmall[.]com, kr-vipsupermarket[.]com, kr-vipthmallshop[.]com, vip-linemall-kr[.]com, vipbuyonline-kr[.]com, vipstore-jp[.]com, buy-ro[.]com, happybuy-kr[.]com, hotsale-ro[.]com, hotstore-jp[.]com, hu-hotmall[.]com, hu-hotsale[.]com, hu-store[.]com, hyviips[.]com, japanmall-jp[.]com, jpshopmall-jp[.]com, kr-vipbuymall[.]com, kr-vipbuyone[.]com, kr-vipbuyonline[.]com, kr-viphotsale[.]com, kr-vipkrstore[.]com, kr-viponlinestore[.]com, mall-ro[.]com, meyou-jp[.]com, mymall-jp[.]com, onlinevipmall-kr[.]com, shopvip-th[.]com, todaysale-jp[.]com, vipluckybuy-jp[.]com, 365day-jp[.]com, 7iqead[.]com, buyakx[.]com, hu-vipmall[.]com, kr-linemall[.]com, kr-vipbigmall[.]com, kr-vipbuyshop[.]com, kr-vipbuytop[.]com, kr-vipgoodbuy[.]com, kr-viphappybuy[.]com, kr-viphotstore[.]com, kr-vipsaleshop[.]com, kr-vipshoping[.]com, kr-vipshopline[.]com, kr-viptodaysale[.]com, linemall-kr[.]com, lubuys[.]com, mallnxj[.]com, pl-todaysale[.]com, shopyvip-tw[.]com, supermarket-tw[.]com, uyeqa2[.]com, vip-linebuy-kr[.]com, vipmall-th[.]com, 365shopping-pl[.]com, 8jadfaw[.]com, bigsale-ro[.]com, buy-pl[.]com, buyjsn[.]com, bynsd[.]com, dcikj[.]com, dfesxe[.]com, hu-todaysale[.]com, jpvip-jp[.]com, kr-luckybuy[.]com, kr-onlinevipmall[.]com, kr-vipbuybuybuy[.]com, kr-vipshoptop[.]com, kr-vipsuperhot[.]com, kr-vipsupermall[.]com, lulbuy[.]com, pi-shopvip[.]com, top-kr[.]com, vipmallmall-kr[.]com, aieutw3[.]com, ashopou[.]com, dsebea[.]com, hotmall-hu[.]com, hotmall-pl[.]com, hotsale-pl[.]com, hrtyrge[.]com, hu-vipstore[.]com, jp-shop-jp[.]com, kr-365vipmall[.]com, kr-vipmymall[.]com, kr-vipmystore[.]com, kr-viptejiashop[.]com, luckybuy-jp[.]com, mgdert[.]com, shopvip-jp[.]com, vip-hotbuy-kr[.]com, vip-lineshop-kr[.]com, vipdiscount-kr[.]com, zbgde[.]com, aiagaw4[.]com, auyshop[.]com, bestselling-pl[.]com, goodshop-jp[.]com, hu-hot[.]com, hu-vipshop[.]com, kaid-th[.]com, kr-happybuy[.]com, kr-vipbuysale[.]com, kr-vipbuyvip[.]com, kr-vipjinrisale[.]com, kr-vipkrshopping[.]com, kr-viponlineshop[.]com, kr-vipsalestore[.]com, linebuy-kr[.]com, luckybuy-kr[.]com, mchmall[.]com, onlineuw[.]com, shoping-jp[.]com, viphappybuy-jp[.]com, viphappybuy-kr[.]com, vipshop-jp[.]com, vipshopline-jp[.]com, vipshopline-kr[.]com, 365shop-pl[.]com, 90sale-pl[.]com, aaa-pl[.]com, buyosd[.]com, discount-kr[.]com, fanjda[.]com, gr-todaysale[.]com, hu-shopvip[.]com, jp-shopbuy[.]com, kr-vipgimall[.]com, kr-vipinhotsale[.]com, kr-vipshopshop[.]com, kr-vipsupershop[.]com, kr-vipsuperstore[.]com, mlumall[.]com, pl-hot[.]com, pl-hotsale[.]com, ro-todaysale-ro[.]com, shopvip-tw[.]com, thmallshop-jp[.]com, vipgoodbuy-jp[.]com, vipgoodbuy-kr[.]com, buymxj[.]com, firnvse[.]com, hotshopping-ro[.]com, japanstore-jp[.]com, uaeioa2[.]com | 174 e-commerce scam websites |








